Logto es una alternativa a Auth0 diseñada para aplicaciones modernas y productos SaaS. Ofrece servicios tanto de Cloud como de código abierto para ayudarte a lanzar rápidamente tu sistema de gestión e identidad (IAM). Disfruta de autenticación, autorización y gestión multi-tenant todo en uno.
Recomendamos comenzar con un tenant de desarrollo gratuito en Logto Cloud. Esto te permite explorar todas las características fácilmente.
En este artículo, repasaremos los pasos para construir rápidamente la experiencia de inicio de sesión de SendGrid (autenticación de usuario) con Expo (React Native) y Logto.
Requisitos previos
- Una instancia de Logto en funcionamiento. Consulta la página de introducción para comenzar.
- Conocimientos básicos de Expo (React Native).
- Una cuenta de SendGrid utilizable.
Crear una aplicación en Logto
Logto se basa en la autenticación OpenID Connect (OIDC) y la autorización OAuth 2.0. Admite la gestión de identidad federada a través de múltiples aplicaciones, comúnmente llamada inicio de sesión único (SSO).
Para crear tu aplicación Native app, simplemente sigue estos pasos:
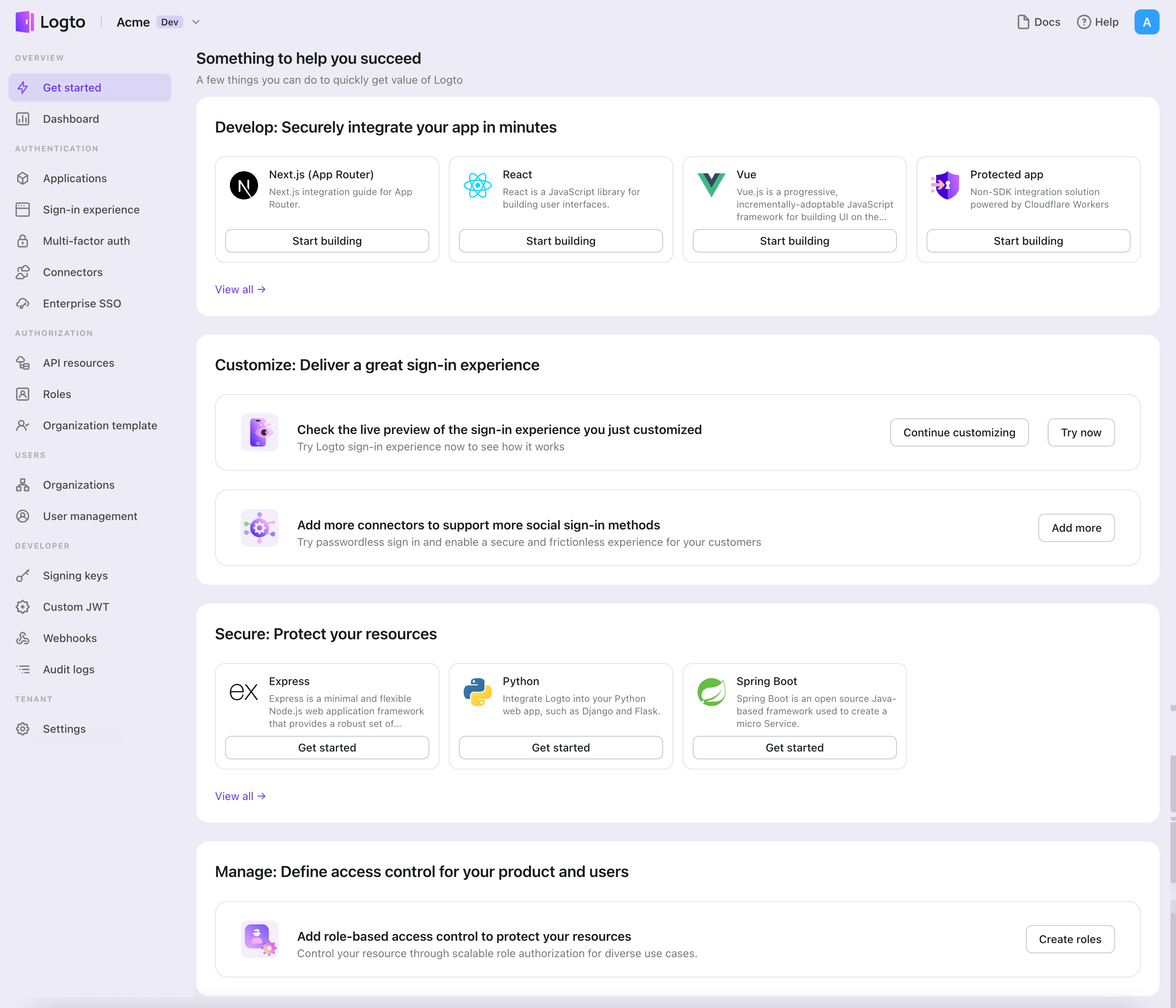
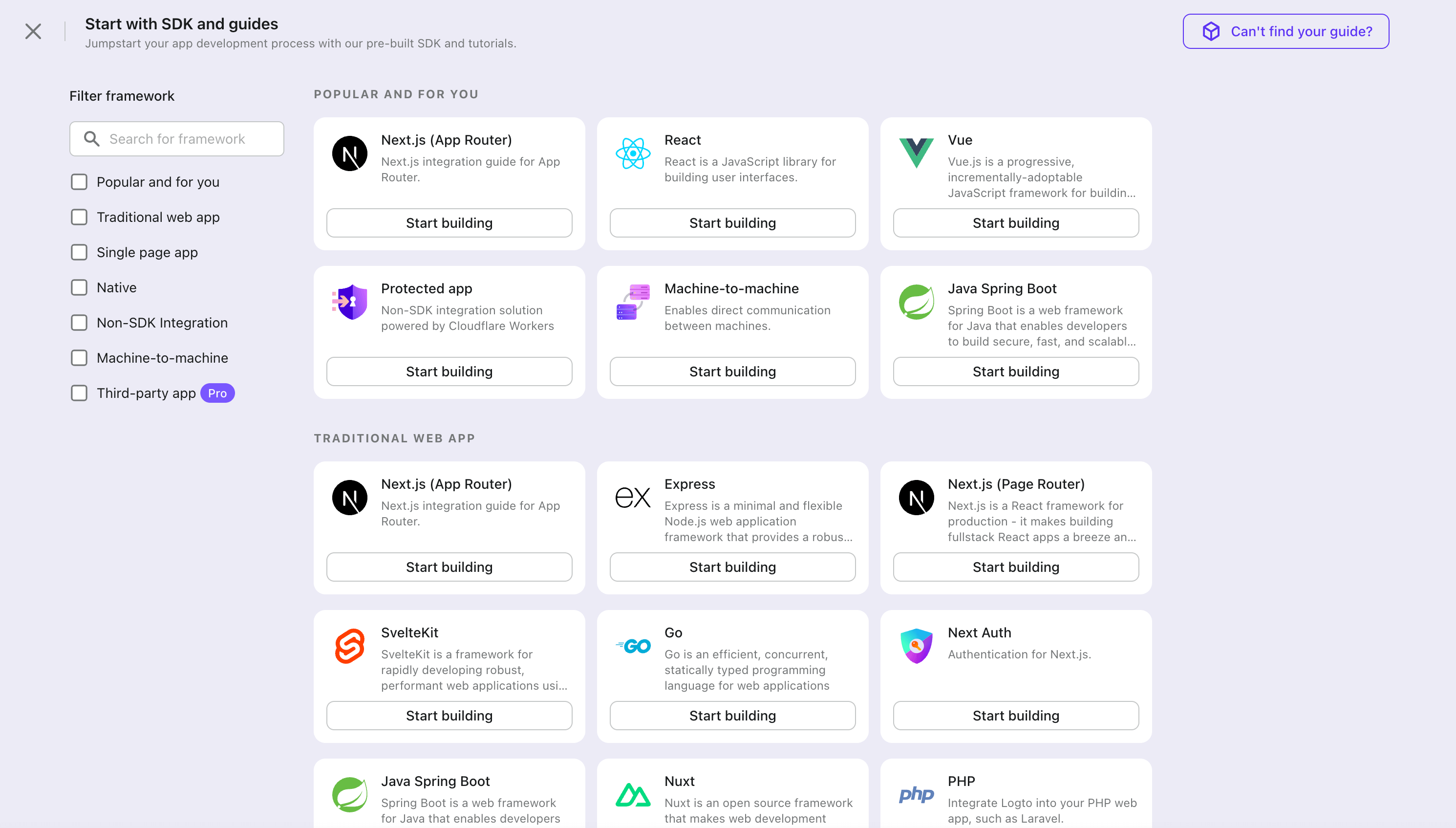
- Abre la Consola de Logto. En la sección "Comenzar", haz clic en el enlace "Ver todo" para abrir la lista de marcos de aplicaciones. Alternativamente, puedes navegar a Consola de Logto > Aplicaciones, y hacer clic en el botón "Crear aplicación".
- En el modal que se abre, haz clic en la sección "Native app" o filtra todos los marcos "Native app" disponibles usando las casillas de filtro rápido a la izquierda. Haz clic en la tarjeta del marco "Expo" para comenzar a crear tu aplicación.
- Ingresa el nombre de la aplicación, por ejemplo, "Librería", y haz clic en "Crear aplicación".
🎉 ¡Ta-da! Acabas de crear tu primera aplicación en Logto. Verás una página de felicitaciones que incluye una guía de integración detallada. Sigue la guía para ver cómo será la experiencia en tu aplicación.
Integrar Logto SDK
- La siguiente demostración está construida sobre Expo ~50.0.6.
- El proyecto de ejemplo está disponible en nuestro repositorio SDK.
Instalación
Instala Logto SDK y las dependencias pares a través de tu gestor de paquetes favorito:
- npm
- Yarn
- pnpm
npm i @logto/rn
npm i expo-crypto expo-secure-store expo-web-browser @react-native-async-storage/async-storage
yarn add @logto/rn
yarn add expo-crypto expo-secure-store expo-web-browser @react-native-async-storage/async-storage
pnpm add @logto/rn
pnpm add expo-crypto expo-secure-store expo-web-browser @react-native-async-storage/async-storage
El paquete @logto/rn es el SDK para Logto. Los paquetes restantes son sus dependencias pares. No pudieron ser listados como dependencias directas porque el Expo CLI requiere que todas las dependencias para módulos nativos se instalen directamente dentro del package.json del proyecto raíz.
Si estás instalando esto en una aplicación React Native bare, también deberías seguir estas instrucciones de instalación adicionales.
Iniciar el proveedor de Logto
Importa y utiliza LogtoProvider para proporcionar un contexto de Logto:
import { LogtoProvider, LogtoConfig } from '@logto/rn';
const config: LogtoConfig = {
endpoint: '<your-logto-endpoint>',
appId: '<your-application-id>',
};
const App = () => (
<LogtoProvider config={config}>
<YourAppContent />
</LogtoProvider>
);
Implementar inicio y cierre de sesión
Antes de profundizar en los detalles, aquí tienes una visión general rápida de la experiencia del usuario final. El proceso de inicio de sesión se puede simplificar de la siguiente manera:
- Tu aplicación invoca el método de inicio de sesión.
- El usuario es redirigido a la página de inicio de sesión de Logto. Para aplicaciones nativas, se abre el navegador del sistema.
- El usuario inicia sesión y es redirigido de vuelta a tu aplicación (configurada como el URI de redirección).
Sobre el inicio de sesión basado en redirección
- Este proceso de autenticación sigue el protocolo OpenID Connect (OIDC), y Logto aplica medidas de seguridad estrictas para proteger el inicio de sesión del usuario.
- Si tienes múltiples aplicaciones, puedes usar el mismo proveedor de identidad (Logto). Una vez que el usuario inicia sesión en una aplicación, Logto completará automáticamente el proceso de inicio de sesión cuando el usuario acceda a otra aplicación.
Para aprender más sobre la lógica y los beneficios del inicio de sesión basado en redirección, consulta Experiencia de inicio de sesión de Logto explicada.
Cambia a la página de detalles de la aplicación de Logto Console. Añade un URI de redirección nativo (por ejemplo, io.logto://callback), luego haz clic en "Guardar".
-
Para iOS, el esquema del URI de redirección realmente no importa ya que la clase
ASWebAuthenticationSessionescuchará el URI de redirección independientemente de si está registrado. -
Para Android, el esquema del URI de redirección debe completarse en el archivo
app.jsonde Expo, por ejemplo:app.json{
"expo": {
"scheme": "io.logto"
}
}
Ahora de vuelta a tu aplicación, puedes usar el hook useLogto para iniciar y cerrar sesión:
import { useLogto } from '@logto/rn';
import { Button } from 'react-native';
const Content = () => {
const { signIn, signOut, isAuthenticated } = useLogto();
return (
<div>
{isAuthenticated ? (
<Button title="Cerrar sesión" onPress={async () => signOut()} />
) : (
// Reemplaza el URI de redirección con el tuyo propio
<Button title="Iniciar sesión" onPress={async () => signIn('io.logto://callback')} />
)}
</div>
);
};
Punto de control: Prueba tu aplicación
Ahora, puedes probar tu aplicación:
- Ejecuta tu aplicación, verás el botón de inicio de sesión.
- Haz clic en el botón de inicio de sesión, el SDK iniciará el proceso de inicio de sesión y te redirigirá a la página de inicio de sesión de Logto.
- Después de iniciar sesión, serás redirigido de vuelta a tu aplicación y verás el botón de cierre de sesión.
- Haz clic en el botón de cierre de sesión para limpiar el almacenamiento de tokens y cerrar sesión.
Añadir conector SendGrid
El conector Email es un método utilizado para enviar contraseñas de un solo uso (OTPs) para la autenticación. Permite la verificación de Dirección de correo electrónico para admitir la autenticación sin contraseña, incluyendo el registro basado en Email, inicio de sesión, autenticación de dos factores (2FA) y recuperación de cuenta. Puedes conectar fácilmente SendGrid como tu proveedor de Email. Con el conector Email de Logto, puedes configurarlo en solo unos minutos.
Para añadir un conector Email, simplemente sigue estos pasos:
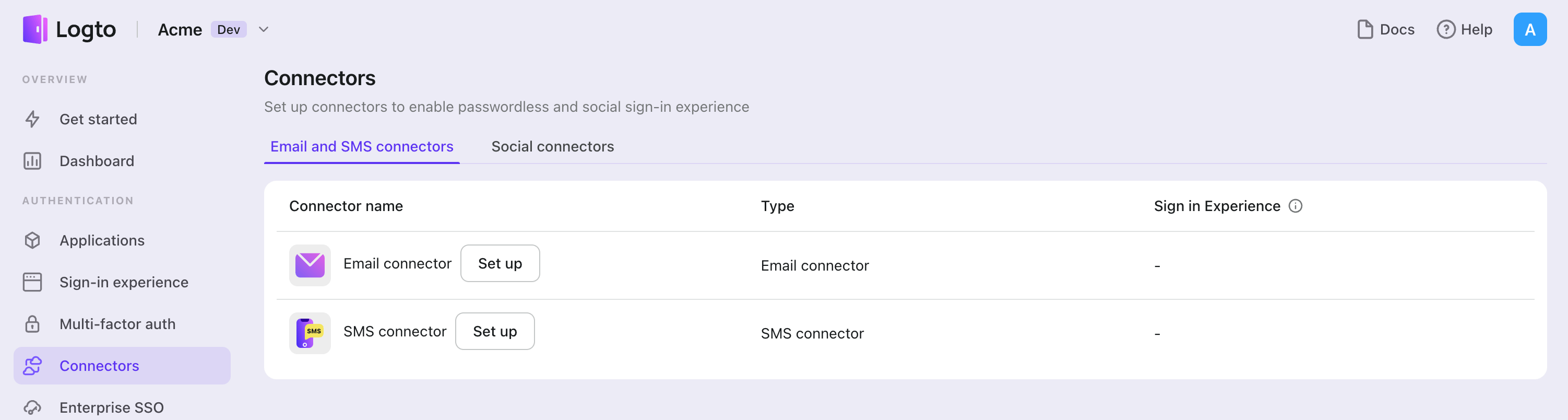
- Navega a Console > Connector > Email and SMS connectors.
- Para añadir un nuevo conector Email, haz clic en el botón "Set up" y selecciona "SendGrid".
- Revisa la documentación README para tu proveedor seleccionado.
- Completa los campos de configuración en la sección "Parameter Configuration".
- Personaliza la plantilla Email utilizando el editor JSON.
- Prueba tu configuración enviando un código de verificación a tu Dirección de correo electrónico.
Si estás siguiendo la guía del Conector en el lugar, puedes omitir la siguiente sección.
Configurar Conector de correo electrónico SendGrid
Registrar cuenta de SendGrid
Crea una nueva cuenta en el sitio web de SendGrid. Puedes omitir este paso si ya tienes una cuenta.
Verificar remitentes
Ve a la página de consola de SendGrid e inicia sesión con tu cuenta de SendGrid.
Los remitentes indican las direcciones desde las cuales se enviará nuestro correo electrónico de código de verificación. Para enviar correos electrónicos a través del servidor de correo de SendGrid, necesitas verificar al menos un remitente.
Desde la página de consola de SendGrid, ve a "Settings" -> "Sender Authentication" desde la barra lateral.
La autenticación de dominio es recomendada pero no obligatoria. Puedes hacer clic en "Get started" en la tarjeta "Authenticate Your Domain" y seguir la guía que aparece para vincular y verificar un remitente en SendGrid.
Al hacer clic en el botón "Verify a Single Sender" en el panel, ahora te enfocarás en un formulario que requiere información crítica para crear un remitente. Sigue la guía, completa todos estos campos y presiona el botón "Create".
Después de crear el remitente único, se debería enviar un correo electrónico con un enlace de verificación a la dirección de correo electrónico de tu remitente. Ve a tu buzón, encuentra el correo de verificación y termina de verificar el remitente único haciendo clic en el enlace proporcionado en el correo electrónico. Ahora puedes enviar correos electrónicos a través del conector de SendGrid usando el remitente que acabas de verificar.
Crear claves de API
Comencemos desde la página de consola de SendGrid, ve a "Settings" -> "API Keys" desde la barra lateral.
Haz clic en "Create API Key" en la esquina superior derecha de la página de API Keys. Escribe el nombre de la clave de API y personaliza "API Key Permission" según tu caso de uso. Se requiere un acceso global Full Access o Restricted Access con acceso completo a Mail Send antes de enviar correos electrónicos con esta clave de API.
La clave de API se te presenta en la pantalla tan pronto como terminas el proceso de Create API Key. Debes guardar esta clave de API en un lugar seguro porque esta es la única oportunidad que tienes para verla.
Configurar tu conector
Completa el campo apiKey con la clave de API creada en la sección "Crear claves de API".
Completa los campos fromEmail y fromName con la From Address y el Nickname de los remitentes. Puedes encontrar los detalles del remitente en la página "Sender Management". fromName es OPCIONAL, por lo que puedes omitirlo.
Puedes agregar múltiples plantillas de conector de correo de SendGrid para diferentes casos. Aquí tienes un ejemplo de cómo agregar una sola plantilla:
- Completa el campo
subject, que funciona como el título de los correos electrónicos. - Completa el campo
contentcon contenidos de tipo cadena arbitraria. No olvides dejar el marcador de posición{{code}}para el código de verificación aleatorio. - Completa el campo
usageTypeconRegister,SignIn,ForgotPassword,Genericpara diferentes casos de uso. - Completa el campo
typecontext/plainotext/htmlpara diferentes tipos de contenido.
Para habilitar flujos completos de usuario, se requieren plantillas con usageType Register, SignIn, ForgotPassword y Generic.
Aquí tienes un ejemplo de JSON de plantilla de conector de SendGrid.
[
{
"subject": "<register-template-subject>",
"content": "<Logto: Your verification code is {{code}}. (register template)>",
"usageType": "Register",
"type": "text/plain",
},
{
"subject": "<sign-in-template-subject>",
"content": "<Logto: Your verification code is {{code}}. (sign-in template)>",
"usageType": "SignIn",
"type": "text/plain",
},
{
"subject": "<forgot-password-template-subject>",
"content": "<Logto: Your verification code is {{code}}. (forgot-password template)>",
"usageType": "ForgotPassword",
"type": "text/plain",
},
{
"subject": "<generic-template-subject>",
"content": "<Logto: Your verification code is {{code}}. (generic template)>",
"usageType": "Generic",
"type": "text/plain",
},
]
Probar el conector de correo electrónico de SendGrid
Puedes escribir una dirección de correo electrónico y hacer clic en "Send" para ver si la configuración funciona antes de "Save and Done".
Eso es todo. No olvides habilitar el conector en la experiencia de inicio de sesión
Tipos de configuración
| Nombre | Tipo |
|---|---|
| apiKey | string |
| fromEmail | string |
| fromName | string (OPCIONAL) |
| templates | Template[] |
| Propiedades de la plantilla | Tipo | Valores del enum |
|---|---|---|
| subject | string | N/A |
| content | string | N/A |
| usageType | enum string | 'Register' | 'SignIn' | 'ForgotPassword' | 'Generic' |
| type | enum string | 'text/plain' | 'text/html' |
Guarda tu configuración
Verifica que hayas completado los valores necesarios en el área de configuración del conector Logto. Haz clic en "Guardar y listo" (o "Guardar cambios") y el conector SendGrid debería estar disponible ahora.
Habilitar el conector SendGrid en la Experiencia de inicio de sesión
Una vez que crees un conector con éxito, puedes habilitar el inicio de sesión y registro sin contraseña basado en número de teléfono.
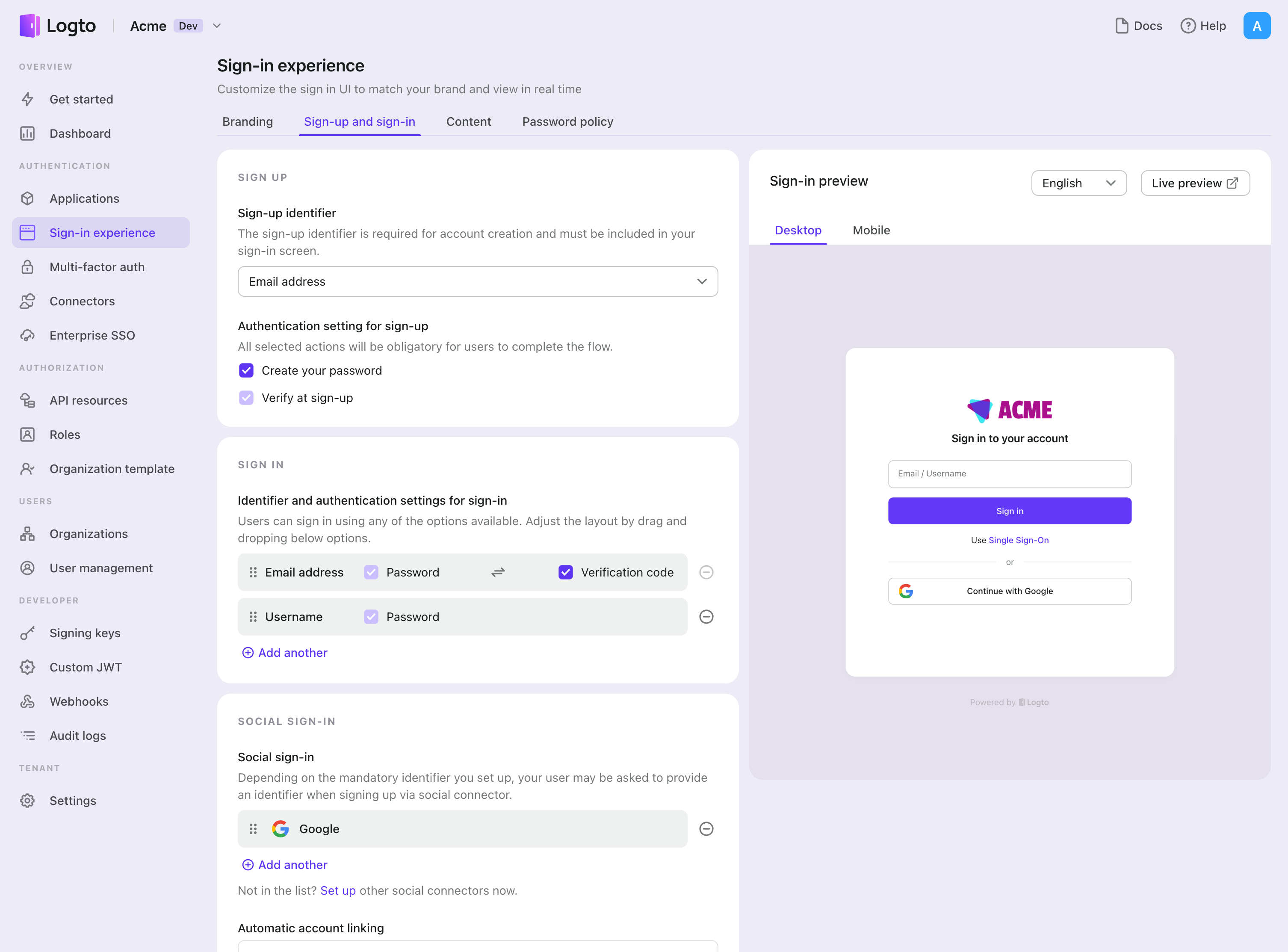
- Navega a Consola > Experiencia de inicio de sesión > Registro e inicio de sesión.
- Configura los métodos de registro (Opcional):
- Selecciona "Dirección de correo electrónico" o "Correo electrónico o número de teléfono" como el identificador de registro.
- "Verificar al registrarse" se fuerza a estar habilitado. También puedes habilitar "Crear una contraseña" en el registro.
- Configura los métodos de inicio de sesión:
- Selecciona Dirección de correo electrónico como uno de los identificadores de inicio de sesión. Puedes proporcionar múltiples identificadores disponibles (correo electrónico, número de teléfono y nombre de usuario).
- Selecciona "Código de verificación" y / o "Contraseña" como el factor de autenticación.
- Haz clic en "Guardar cambios" y pruébalo en "Vista previa en vivo".
Además del registro e inicio de sesión a través de OTPs de , también puedes tener habilitada la recuperación de contraseña y la verificación de seguridad basada en , así como vincular Dirección de correo electrónico al perfil. Consulta Flujos de usuario final para más detalles.
Pruebas y Validación
Regresa a tu aplicación Expo (React Native). Ahora deberías poder iniciar sesión con SendGrid. ¡Disfruta!
Lecturas adicionales
Flujos de usuario final: Logto proporciona flujos de autenticación listos para usar, incluyendo MFA y SSO empresarial, junto con potentes APIs para la implementación flexible de configuraciones de cuenta, verificación de seguridad y experiencia multi-tenant.
Autorización (Authorization): La autorización define las acciones que un usuario puede realizar o los recursos a los que puede acceder después de ser autenticado. Explora cómo proteger tu API para aplicaciones nativas y de una sola página e implementar el Control de Acceso Basado en Roles (RBAC).
Organizaciones (Organizations): Particularmente efectivo en aplicaciones SaaS multi-tenant y B2B, la función de organización permite la creación de inquilinos, gestión de miembros, RBAC a nivel de organización y aprovisionamiento justo a tiempo.
Serie IAM del cliente: Nuestros artículos de blog en serie sobre la Gestión de Identidad y Acceso del Cliente (o Consumidor), desde los conceptos básicos hasta temas avanzados y más allá.