Logto は、モダンなアプリや SaaS 製品向けに設計された Auth0 の代替です。 Cloud と オープンソース の両方のサービスを提供し、アイデンティティと管理 (IAM) システムを迅速に立ち上げるのに役立ちます。認証 (Authentication)、認可 (Authorization)、マルチテナント管理を すべて一つに まとめて楽しんでください。
Logto Cloud で無料の開発テナントから始めることをお勧めします。これにより、すべての機能を簡単に探索できます。
この記事では、.NET Core (Blazor Server) と Logto を使用して、AWS SES サインイン体験(ユーザー認証 (Authentication))を迅速に構築する手順を説明します。
前提条件
- 稼働中の Logto インスタンス。紹介ページ をチェックして始めてください。
- .NET Core (Blazor Server) の基本的な知識。
- 使用可能な AWS SES アカウント。
Logto にアプリケーションを作成する
Logto は OpenID Connect (OIDC) 認証 (Authentication) と OAuth 2.0 認可 (Authorization) に基づいています。これは、複数のアプリケーション間でのフェデレーテッドアイデンティティ管理をサポートし、一般的にシングルサインオン (SSO) と呼ばれます。
あなたの Traditional web アプリケーションを作成するには、次の手順に従ってください:
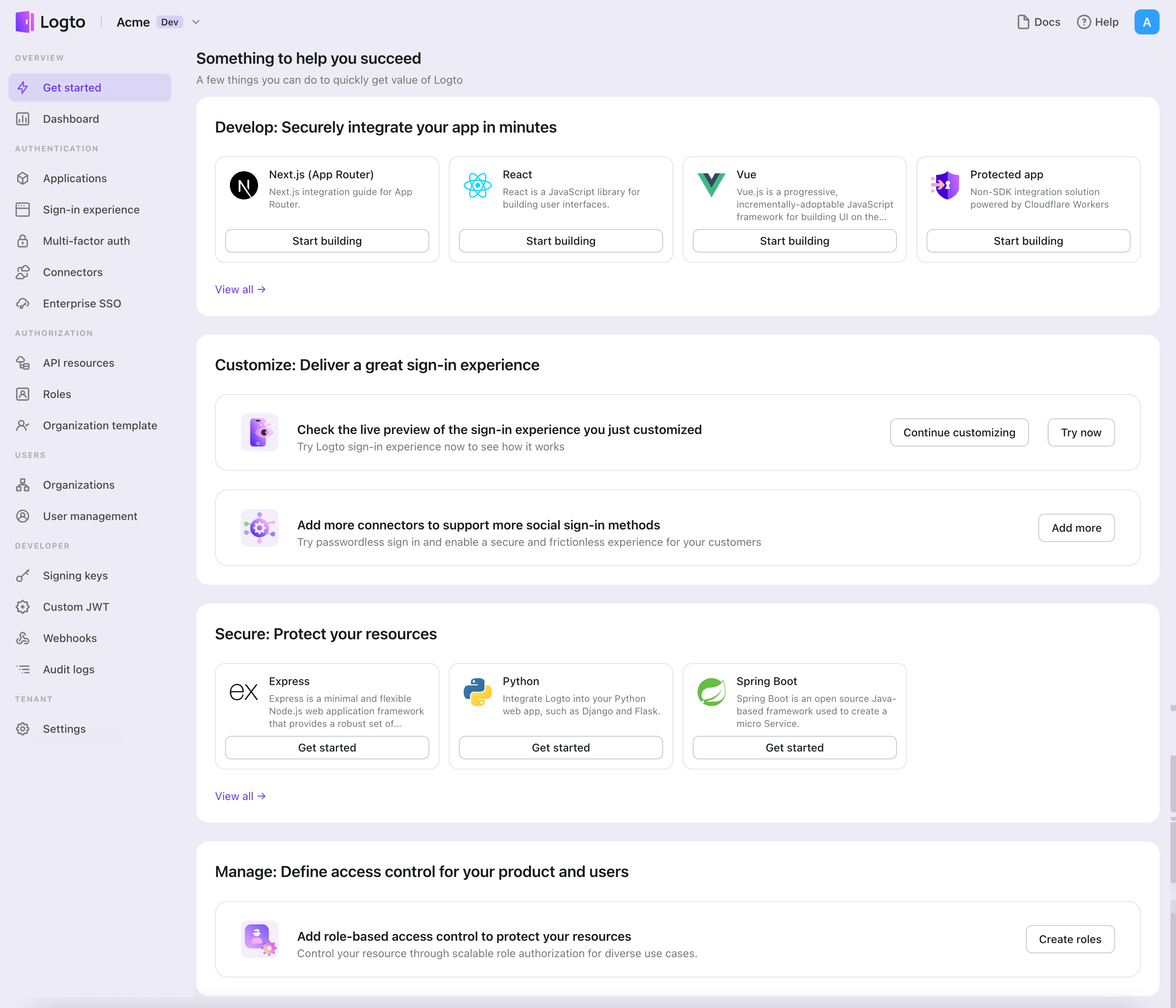
- Logto コンソール を開きます。「Get started」セクションで、「View all」リンクをクリックしてアプリケーションフレームワークのリストを開きます。あるいは、Logto Console > Applications に移動し、「Create application」ボタンをクリックします。
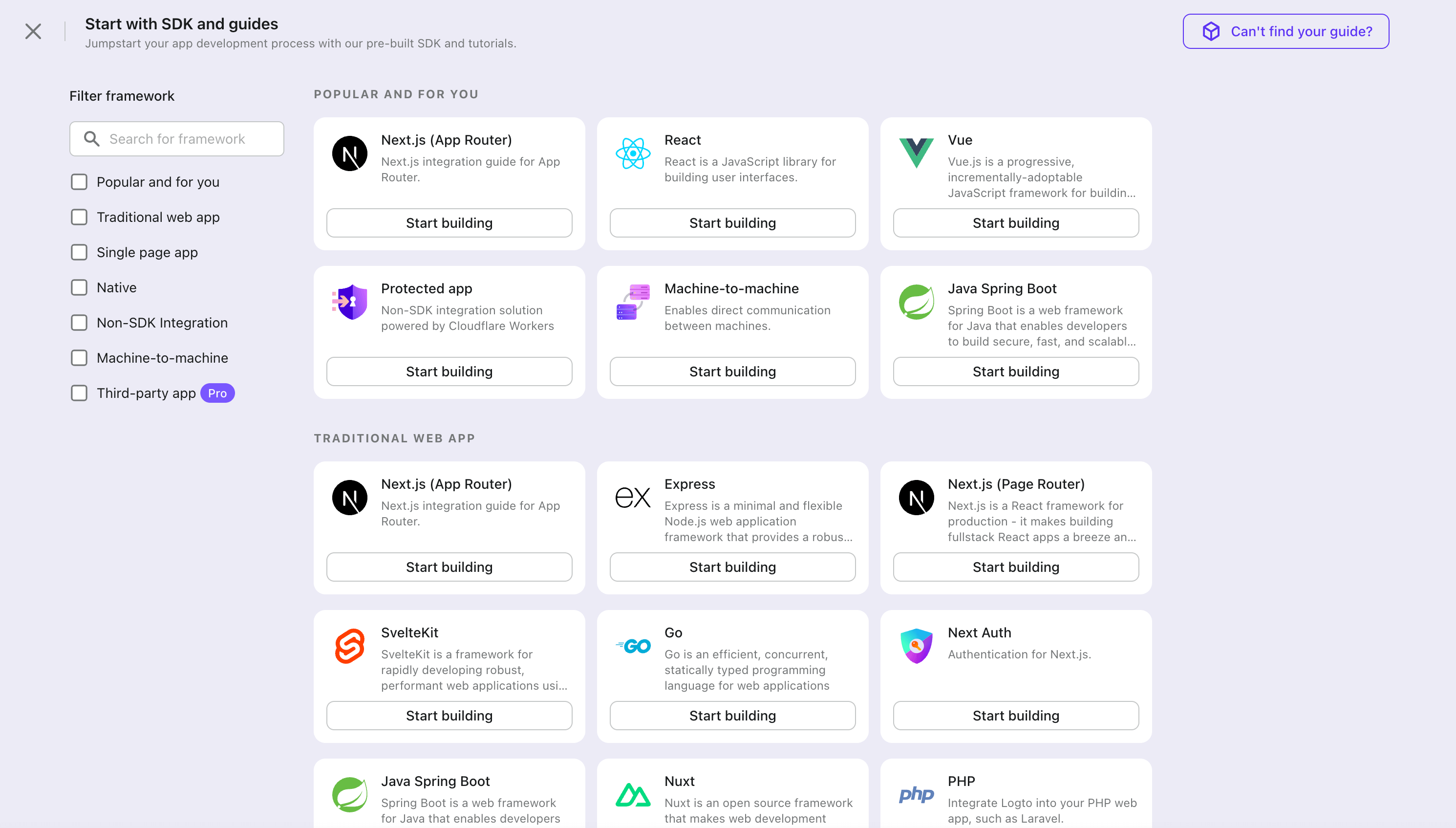
- 開いたモーダルで、左側のクイックフィルターチェックボックスを使用して、利用可能なすべての "Traditional web" フレームワークをフィルタリングするか、"Traditional web" セクションをクリックします。".Net Core (Blazor Server)" フレームワークカードをクリックして、アプリケーションの作成を開始します。
- アプリケーション名を入力します。例:「Bookstore」と入力し、「Create application」をクリックします。
🎉 タダーン!Logto で最初のアプリケーションを作成しました。詳細な統合ガイドを含むお祝いページが表示されます。ガイドに従って、アプリケーションでの体験を確認してください。
Logto SDK を統合する
- 次のデモンストレーションは .NET Core 8.0 を基に構築されています。SDK は .NET 6.0 以上に対応しています。
- .NET Core のサンプルプロジェクトは GitHub リポジトリ で利用可能です。
インストール
プロジェクトに NuGet パッケージを追加します:
dotnet add package Logto.AspNetCore.Authentication
Logto 認証 (Authentication) を追加する
Startup.cs(または Program.cs)を開き、次のコードを追加して Logto 認証 (Authentication) サービスを登録します:
using Logto.AspNetCore.Authentication;
var builder = WebApplication.CreateBuilder(args);
builder.Services.AddLogtoAuthentication(options =>
{
options.Endpoint = builder.Configuration["Logto:Endpoint"]!;
options.AppId = builder.Configuration["Logto:AppId"]!;
options.AppSecret = builder.Configuration["Logto:AppSecret"];
});
AddLogtoAuthentication メソッドは次のことを行います:
- デフォルトの認証 (Authentication) スキームを
LogtoDefaults.CookieSchemeに設定します。 - デフォルトのチャレンジスキームを
LogtoDefaults.AuthenticationSchemeに設定します。 - デフォルトのサインアウトスキームを
LogtoDefaults.AuthenticationSchemeに設定します。 - 認証 (Authentication) スキームにクッキーと OpenID Connect 認証 (Authentication) ハンドラーを追加します。
サインインおよびサインアウトフロー
進む前に、.NET Core 認証 (Authentication) ミドルウェアにおける混乱しやすい用語を 2 つ明確にする必要があります:
- CallbackPath: ユーザーがサインインした後に Logto がユーザーをリダイレクトする URI (Logto における「リダイレクト URI」)
- RedirectUri: Logto 認証 (Authentication) ミドルウェアで必要なアクションが実行された後にリダイレクトされる URI
サインインプロセスは次のように示されます:
同様に、.NET Core にはサインアウトフローのための SignedOutCallbackPath と RedirectUri もあります。
明確にするために、これらを次のように呼びます:
| 使用する用語 | .NET Core 用語 |
|---|---|
| Logto リダイレクト URI | CallbackPath |
| Logto サインアウト後リダイレクト URI | SignedOutCallbackPath |
| アプリケーションリダイレクト URI | RedirectUri |
リダイレクトベースのサインインについて
- この認証 (Authentication) プロセスは OpenID Connect (OIDC) プロトコルに従い、Logto はユーザーのサインインを保護するために厳格なセキュリティ対策を講じています。
- 複数のアプリがある場合、同じアイデンティティプロバイダー (Logto) を使用できます。ユーザーがあるアプリにサインインすると、Logto は別のアプリにアクセスした際に自動的にサインインプロセスを完了します。
リダイレクトベースのサインインの理論と利点について詳しく知るには、Logto サインイン体験の説明を参照してください。
リダイレクト URI を設定する
以下のコードスニペットでは、あなたのアプリが http://localhost:3000/ で実行されていると仮定しています。
まず、Logto リダイレクト URI を設定しましょう。次の URI を Logto アプリケーション詳細ページの「リダイレクト URI」リストに追加します:
http://localhost:3000/Callback
Logto サインアウト後リダイレクト URI を設定するには、次の URI を Logto アプリケーション詳細ページの「サインアウト後リダイレクト URI」リストに追加します:
http://localhost:3000/SignedOutCallback
デフォルトパスを変更する
Logto リダイレクト URI にはデフォルトパス /Callback があり、Logto サインアウト後リダイレクト URI にはデフォルトパス /SignedOutCallback があります。
特別な要件がない場合は、そのままにしておくことができます。変更したい場合は、LogtoOptions の CallbackPath と SignedOutCallbackPath プロパティを設定できます:
builder.Services.AddLogtoAuthentication(options =>
{
// 他の設定...
options.CallbackPath = "/Foo";
options.SignedOutCallbackPath = "/Bar";
});
Logto アプリケーション詳細ページの値もそれに応じて更新することを忘れないでください。
ルートを追加する
Blazor Server は SignalR を使用してサーバーとクライアント間で通信するため、HTTP コンテキストを直接操作するメソッド(チャレンジやリダイレクトの発行など)は、Blazor コンポーネントから呼び出された場合、期待通りに動作しません。
これを正しく行うためには、サインインとサインアウトのリダイレクト用に 2 つのエンドポイントを明示的に追加する必要があります:
app.MapGet("/SignIn", async context =>
{
if (!(context.User?.Identity?.IsAuthenticated ?? false))
{
await context.ChallengeAsync(new AuthenticationProperties { RedirectUri = "/" });
} else {
context.Response.Redirect("/");
}
});
app.MapGet("/SignOut", async context =>
{
if (context.User?.Identity?.IsAuthenticated ?? false)
{
await context.SignOutAsync(new AuthenticationProperties { RedirectUri = "/" });
} else {
context.Response.Redirect("/");
}
});
これで、これらのエンドポイントにリダイレクトしてサインインとサインアウトをトリガーできます。
サインイン / サインアウトボタンを実装する
Razor コンポーネントに次のコードを追加します:
@using Microsoft.AspNetCore.Components.Authorization
@using System.Security.Claims
@inject AuthenticationStateProvider AuthenticationStateProvider
@inject NavigationManager NavigationManager
@* ... *@
<p>認証 (Authentication) 済み: @User.Identity?.IsAuthenticated</p>
@if (User.Identity?.IsAuthenticated == true)
{
<button @onclick="SignOut">サインアウト</button>
}
else
{
<button @onclick="SignIn">サインイン</button>
}
@* ... *@
@code {
private ClaimsPrincipal? User { get; set; }
protected override async Task OnInitializedAsync()
{
var authState = await AuthenticationStateProvider.GetAuthenticationStateAsync();
User = authState.User;
}
private void SignIn()
{
NavigationManager.NavigateTo("/SignIn", forceLoad: true);
}
private void SignOut()
{
NavigationManager.NavigateTo("/SignOut", forceLoad: true);
}
}
説明:
- インジェクトされた
AuthenticationStateProviderは、現在のユーザーの認証 (Authentication) 状態を取得し、Userプロパティを設定するために使用されます。 SignInとSignOutメソッドは、それぞれサインインおよびサインアウトのエンドポイントにユーザーをリダイレクトするために使用されます。Blazor Server の性質上、リダイレクションをトリガーするためにNavigationManagerを強制ロードで使用する必要があります。
ページは、ユーザーが認証 (Authentication) されていない場合は「サインイン」ボタンを表示し、認証 (Authentication) されている場合は「サインアウト」ボタンを表示します。
<AuthorizeView /> コンポーネント
代わりに、AuthorizeView コンポーネントを使用して、ユーザーの認証 (Authentication) 状態に基づいてコンテンツを条件付きでレンダリングすることができます。このコンポーネントは、認証 (Authentication) 済みユーザーと未認証ユーザーに異なるコンテンツを表示したい場合に便利です。
Razor コンポーネントに次のコードを追加します:
@using Microsoft.AspNetCore.Components.Authorization
@* ... *@
<AuthorizeView>
<Authorized>
<p>Name: @User?.Identity?.Name</p>
@* 認証 (Authentication) 済みユーザー向けのコンテンツ *@
</Authorized>
<NotAuthorized>
@* 未認証ユーザー向けのコンテンツ *@
</NotAuthorized>
</AuthorizeView>
@* ... *@
AuthorizeView コンポーネントは、Task<AuthenticationState> 型のカスケードパラメーターを必要とします。このパラメーターを取得する直接的な方法は、<CascadingAuthenticationState> コンポーネントを追加することです。ただし、Blazor Server の性質上、レイアウトやルートコンポーネントに単純にコンポーネントを追加することはできません(期待通りに動作しない可能性があります)。代わりに、ビルダー (Program.cs または Startup.cs) に次のコードを追加してカスケードパラメーターを提供します:
builder.Services.AddCascadingAuthenticationState();
その後、AuthorizeView コンポーネントを必要とするすべてのコンポーネントで使用できます。
チェックポイント: アプリケーションをテストする
これで、アプリケーションをテストできます:
- アプリケーションを実行すると、サインインボタンが表示されます。
- サインインボタンをクリックすると、SDK がサインインプロセスを初期化し、Logto のサインインページにリダイレクトされます。
- サインインすると、アプリケーションに戻り、サインアウトボタンが表示されます。
- サインアウトボタンをクリックして、トークンストレージをクリアし、サインアウトします。
AWS SES コネクターを追加する
Email コネクターは、認証 (Authentication) のためにワンタイムパスワード (OTP) を送信するための方法です。これは、Email ベースの登録、サインイン、二要素認証 (2FA)、アカウント回復を含むパスワードレス認証 (Authentication) をサポートするために メールアドレス の確認を可能にします。 Logto の Email コネクターを使用すると、数分でこれを設定できます。
Email コネクターを追加するには、次の手順に従ってください:
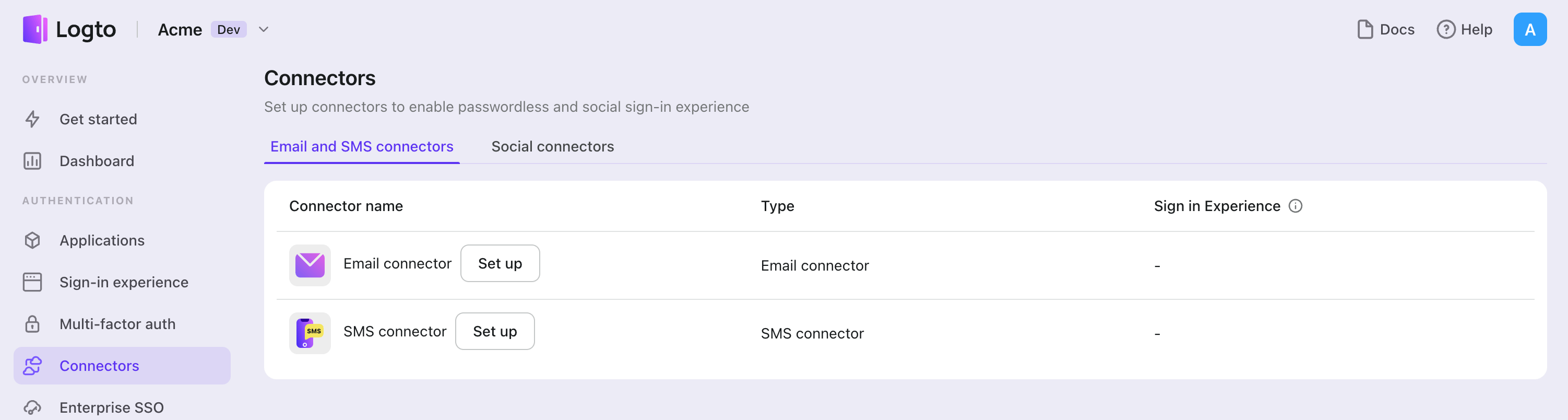
- Console > Connector > Email and SMS connectors に移動します。
- 新しい Email コネクターを追加するには、「Set up」ボタンをクリックし、「AWS SES」を選択します。
- 選択したプロバイダーの README ドキュメントを確認します。
- 「Parameter Configuration」セクションで設定フィールドを完了します。
- JSON エディターを使用して Email テンプレートをカスタマイズします。
- メールアドレス に確認コードを送信して設定をテストします。
インプレースコネクターガイドに従っている場合は、次のセクションをスキップできます。
AWS SES メールコネクター を設定する
AWS サービスコンソールでメールサービスを設定する
AWS アカウントを登録する
AWS にアクセスしてアカウントを登録します。
アイデンティティを作成する
Amazon Simple Email Serviceコンソールに移動します- アイデンティティを作成し、次のオプションのいずれかを選択します
- ドメインを作成する
- メールアドレスを作成する
コネクターの設定
- Amazon コンソールの右上隅にあるユーザー名をクリックして
Security Credentialsに入ります。まだ持っていない場合は、AccessKeyを作成し、慎重に保存してください。 Amazon Simple Email Serviceコネクターの設定を完了します:- ステップ 1 で取得した
AccessKey IDとAccessKey Secretを使用して、それぞれaccessKeyIdとaccessKeySecretを入力します。 region: メール送信に使用するアイデンティティのリージョンをregionフィールドに入力します。emailAddress: メール送信に使用するメールアドレスをLogto\<[email protected]>または\<[email protected]>の形式で入力します。
- ステップ 1 で取得した
以下のパラメーターはオプションです。パラメーターの説明は AWS SES API ドキュメント に記載されています。
feedbackForwardingEmailAddressfeedbackForwardingEmailAddressIdentityArnconfigurationSetName
Amazon SES コネクターをテストする
メールアドレスを入力し、「送信」をクリックして、設定が機能するかどうかを「保存して完了」する前に確認できます。
これで完了です。サインイン体験でコネクターを有効にする のを忘れないでください。
タイプを設定する
| 名前 | タイプ |
|---|---|
| accessKeyId | string |
| accessKeySecret | string |
| region | string |
| emailAddress | string (OPTIONAL) |
| emailAddressIdentityArn | string (OPTIONAL) |
| feedbackForwardingEmailAddress | string (OPTIONAL) |
| feedbackForwardingEmailAddressIdentityArn | string (OPTIONAL) |
| configurationSetName | string (OPTIONAL) |
| templates | Template[] |
| テンプレートプロパティ | タイプ | 列挙値 |
|---|---|---|
| subject | string | N/A |
| content | string | N/A |
| usageType | enum string | 'Register' | 'SignIn' | 'ForgotPassword' | 'Generic' |
設定を保存する
Logto コネクター設定エリアで必要な値をすべて記入したことを確認してください。「保存して完了」または「変更を保存」をクリックすると、AWS SES コネクターが利用可能になります。
サインイン体験で AWS SES コネクターを有効にする
コネクターを正常に作成したら、電話番号ベースのパスワードレスログインと登録を有効にできます。
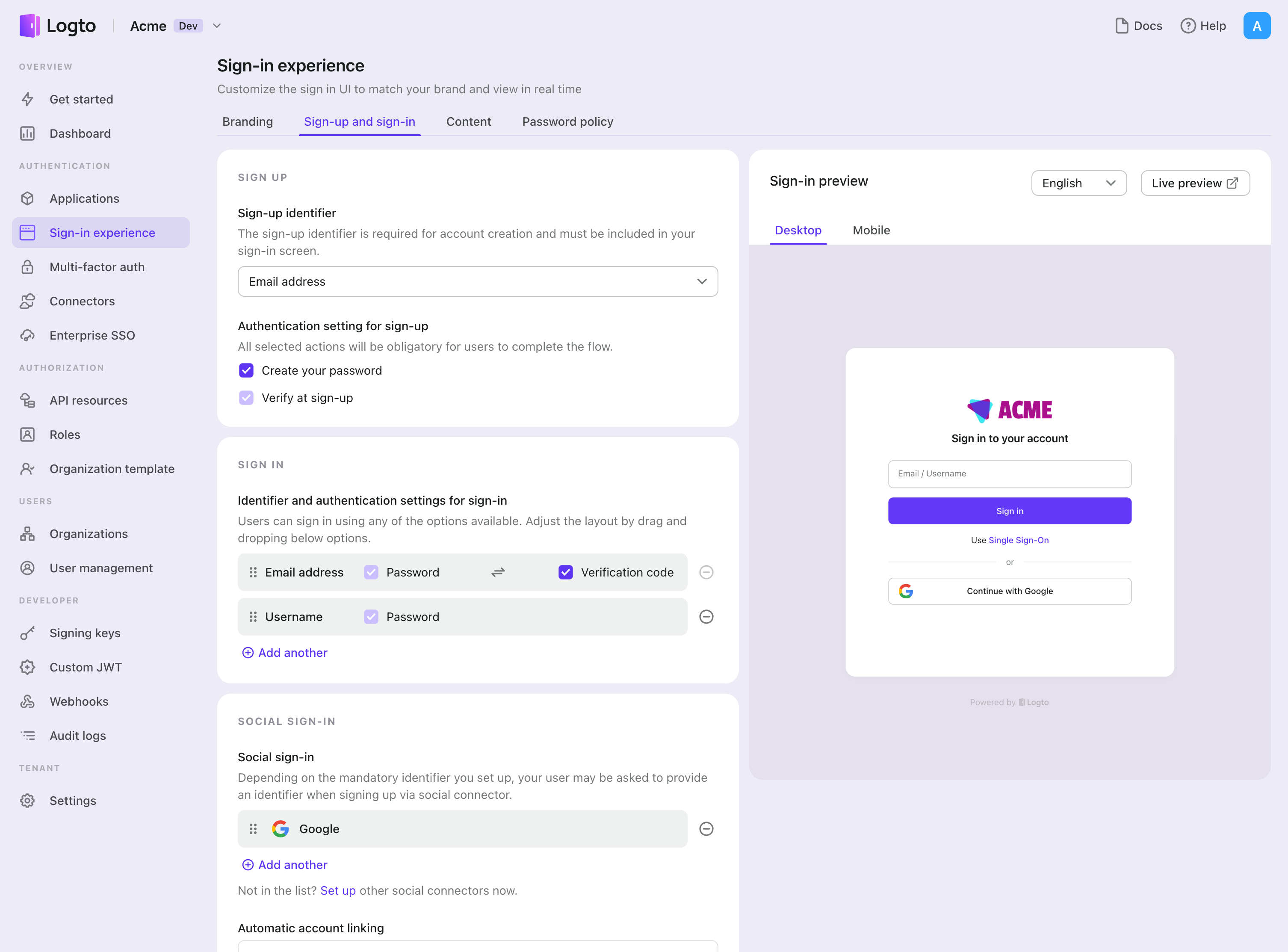
- コンソール > サインイン体験 > サインアップとサインイン に移動します。
- サインアップ方法を設定します(オプション):
- サインアップ識別子として "メールアドレス" または "Email or phone number" を選択します。
- "Verify at sign-up" は強制的に有効化されます。登録時に "Create a password" を有効にすることもできます。
- サインイン方法を設定します:
- サインイン識別子の一つとして メールアドレス を選択します。複数の利用可能な識別子(メール、電話番号、ユーザー名)を提供できます。
- 認証 (Authentication) 要素として "Verification code" および / または "Password" を選択します。
- "Save changes" をクリックし、"Live preview" でテストします。
OTP を使用した登録とログインに加えて、パスワードの回復や ベースのセキュリティ検証を有効にし、メールアドレス をプロファイルにリンクすることもできます。詳細については、エンドユーザーフロー を参照してください。
テストと検証
.NET Core (Blazor Server) アプリに戻ります。これで AWS SES を使用してサインインできるはずです。お楽しみください!
さらなる読み物
エンドユーザーフロー:Logto は、MFA やエンタープライズシングルサインオン (SSO) を含む即時使用可能な認証 (Authentication) フローを提供し、アカウント設定、セキュリティ検証、マルチテナント体験の柔軟な実装のための強力な API を備えています。
認可 (Authorization):認可 (Authorization) は、ユーザーが認証 (Authentication) された後に行えるアクションやアクセスできるリソースを定義します。ネイティブおよびシングルページアプリケーションの API を保護し、ロールベースのアクセス制御 (RBAC) を実装する方法を探ります。
組織 (Organizations):特にマルチテナント SaaS や B2B アプリで効果的な組織機能は、テナントの作成、メンバー管理、組織レベルの RBAC、およびジャストインタイムプロビジョニングを可能にします。
顧客 IAM シリーズ:顧客(または消費者)アイデンティティとアクセス管理に関する連続ブログ投稿で、101 から高度なトピックまでを網羅しています。