Logto es una alternativa a Auth0 diseñada para aplicaciones modernas y productos SaaS. Ofrece servicios tanto de Cloud como de código abierto para ayudarte a lanzar rápidamente tu sistema de gestión e identidad (IAM). Disfruta de autenticación, autorización y gestión multi-tenant todo en uno.
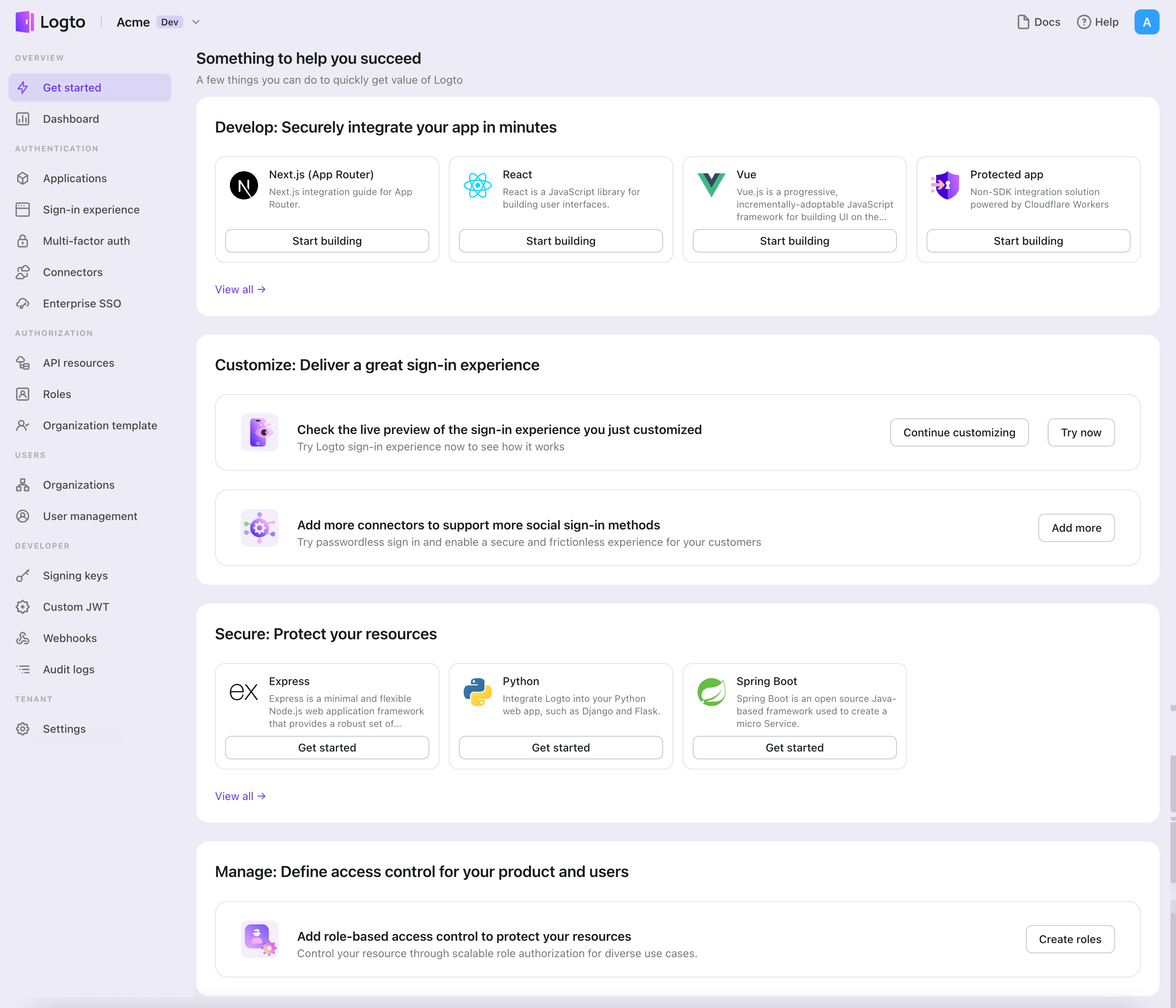
Recomendamos comenzar con un tenant de desarrollo gratuito en Logto Cloud. Esto te permite explorar todas las características fácilmente.
En este artículo, repasaremos los pasos para construir rápidamente la experiencia de inicio de sesión de OIDC (autenticación de usuario) con Next.js (Pages Router) y Logto.
Requisitos previos
- Una instancia de Logto en funcionamiento. Consulta la página de introducción para comenzar.
- Conocimientos básicos de Next.js (Pages Router).
- Una cuenta de OIDC utilizable.
Crear una aplicación en Logto
Logto se basa en la autenticación OpenID Connect (OIDC) y la autorización OAuth 2.0. Admite la gestión de identidad federada a través de múltiples aplicaciones, comúnmente llamada inicio de sesión único (SSO).
Para crear tu aplicación Aplicación web tradicional, simplemente sigue estos pasos:
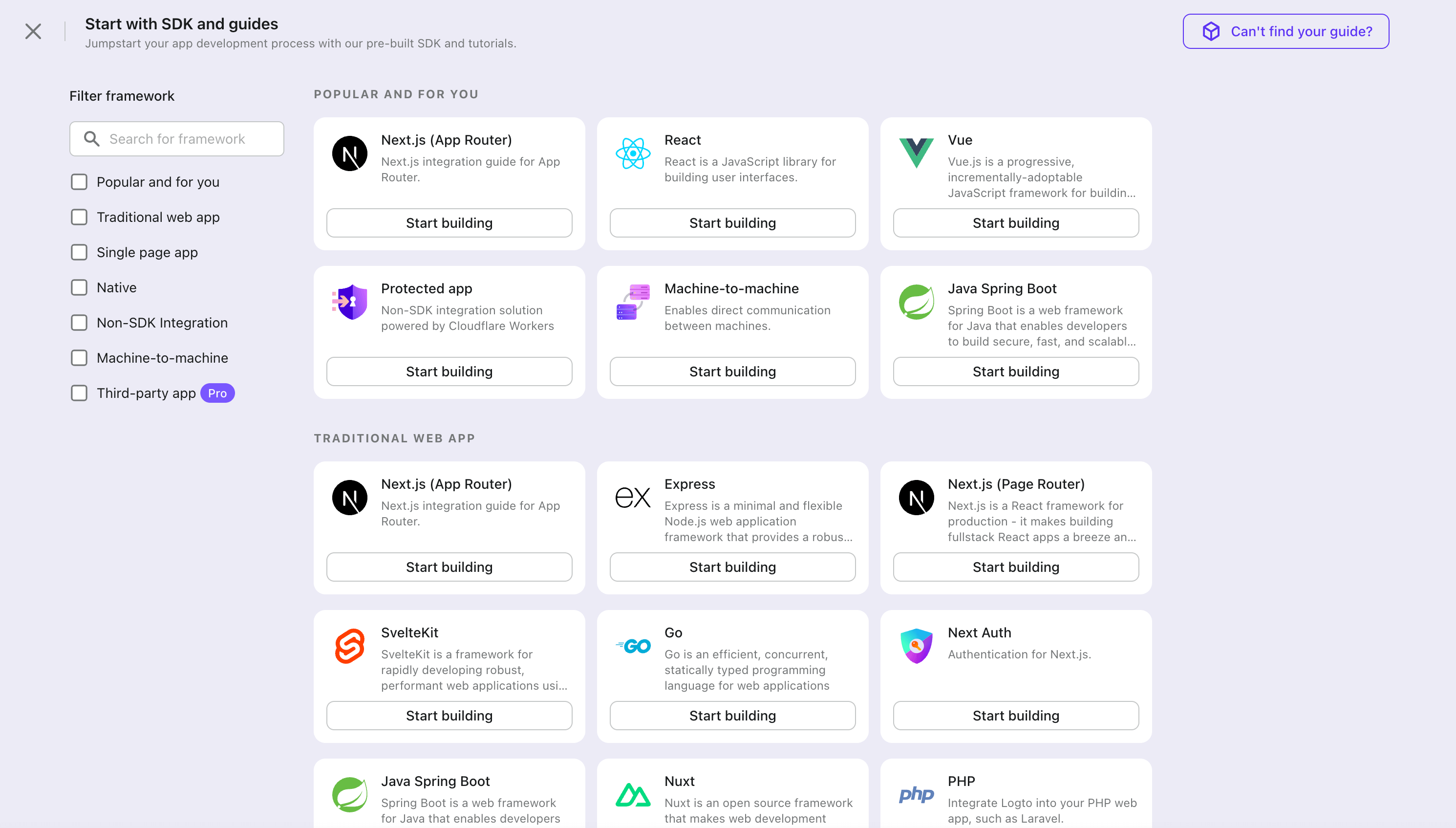
- Abre la Consola de Logto. En la sección "Comenzar", haz clic en el enlace "Ver todo" para abrir la lista de marcos de aplicaciones. Alternativamente, puedes navegar a Consola de Logto > Aplicaciones, y hacer clic en el botón "Crear aplicación".
- En el modal que se abre, haz clic en la sección "Aplicación web tradicional" o filtra todos los marcos "Aplicación web tradicional" disponibles usando las casillas de filtro rápido a la izquierda. Haz clic en la tarjeta del marco "Next.js" para comenzar a crear tu aplicación.
- Ingresa el nombre de la aplicación, por ejemplo, "Librería", y haz clic en "Crear aplicación".
🎉 ¡Ta-da! Acabas de crear tu primera aplicación en Logto. Verás una página de felicitaciones que incluye una guía de integración detallada. Sigue la guía para ver cómo será la experiencia en tu aplicación.
Integrar el SDK de Next.js
- El proyecto de ejemplo está disponible en nuestro repositorio SDK.
- El ejemplo está basado en el Pages Router de Next.js.
Instalación
Instala Logto SDK a través de tu gestor de paquetes favorito:
- npm
- pnpm
- yarn
npm i @logto/nextpnpm add @logto/nextyarn add @logto/nextIntegración
Inicializar LogtoClient
Importa e inicializa LogtoClient:
import LogtoClient from '@logto/next';
export const logtoClient = new LogtoClient({
appId: '<your-application-id>',
appSecret: '<your-app-secret-copied-from-console>',
endpoint: '<your-logto-endpoint>', // Ej. http://localhost:3001
baseUrl: 'http://localhost:3000',
cookieSecret: 'complex_password_at_least_32_characters_long',
cookieSecure: process.env.NODE_ENV === 'production',
});
Configurar URIs de redirección
Antes de profundizar en los detalles, aquí tienes una visión general rápida de la experiencia del usuario final. El proceso de inicio de sesión se puede simplificar de la siguiente manera:
- Tu aplicación invoca el método de inicio de sesión.
- El usuario es redirigido a la página de inicio de sesión de Logto. Para aplicaciones nativas, se abre el navegador del sistema.
- El usuario inicia sesión y es redirigido de vuelta a tu aplicación (configurada como el URI de redirección).
Sobre el inicio de sesión basado en redirección
- Este proceso de autenticación sigue el protocolo OpenID Connect (OIDC), y Logto aplica medidas de seguridad estrictas para proteger el inicio de sesión del usuario.
- Si tienes múltiples aplicaciones, puedes usar el mismo proveedor de identidad (Logto). Una vez que el usuario inicia sesión en una aplicación, Logto completará automáticamente el proceso de inicio de sesión cuando el usuario acceda a otra aplicación.
Para aprender más sobre la lógica y los beneficios del inicio de sesión basado en redirección, consulta Experiencia de inicio de sesión de Logto explicada.
En los siguientes fragmentos de código, asumimos que tu aplicación está ejecutándose en http://localhost:3000/.
Configurar URIs de redirección
Cambia a la página de detalles de la aplicación en Logto Console. Añade una URI de redirección http://localhost:3000/api/logto/sign-in-callback.
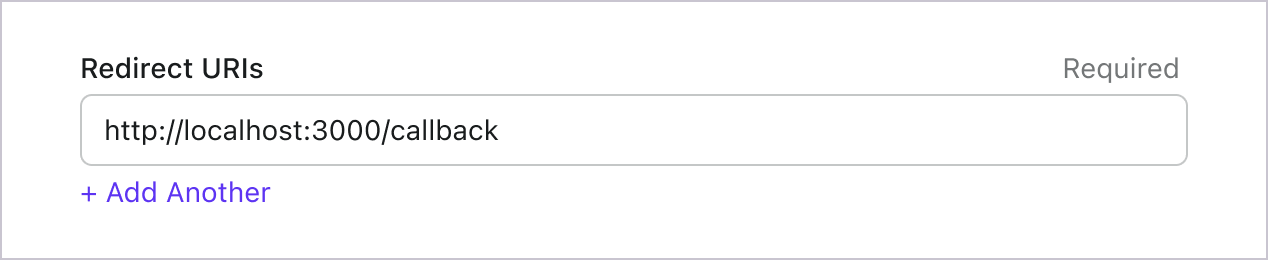
Al igual que al iniciar sesión, los usuarios deben ser redirigidos a Logto para cerrar la sesión de la sesión compartida. Una vez terminado, sería ideal redirigir al usuario de vuelta a tu sitio web. Por ejemplo, añade http://localhost:3000/ como la sección de URI de redirección posterior al cierre de sesión.
Luego haz clic en "Guardar" para guardar los cambios.
Preparar rutas de API
Prepara rutas de API para conectar con Logto.
Regresa a tu IDE/editor, utiliza el siguiente código para implementar primero las rutas de API:
import { logtoClient } from '../../../libraries/logto';
export default logtoClient.handleAuthRoutes();
Esto creará automáticamente 4 rutas:
/api/logto/sign-in: Iniciar sesión con Logto./api/logto/sign-in-callback: Manejar la devolución de llamada de inicio de sesión./api/logto/sign-out: Cerrar sesión con Logto./api/logto/user: Verificar si el usuario está autenticado con Logto, si es así, devolver la información del usuario.
Implementar inicio y cierre de sesión
Hemos preparado las rutas de API, ahora implementemos los botones de inicio y cierre de sesión en tu página de inicio. Necesitamos redirigir al usuario a la ruta de inicio o cierre de sesión cuando sea necesario. Para ayudar con esto, utiliza useSWR para obtener el estado de autenticación desde /api/logto/user.
Consulta esta guía para aprender más sobre useSWR.
import { type LogtoContext } from '@logto/next';
import useSWR from 'swr';
const Home = () => {
const { data } = useSWR<LogtoContext>('/api/logto/user');
return (
<nav>
{data?.isAuthenticated ? (
<p>
Hola, {data.claims?.sub},
<button
onClick={() => {
window.location.assign('/api/logto/sign-out');
}}
>
Cerrar sesión
</button>
</p>
) : (
<p>
<button
onClick={() => {
window.location.assign('/api/logto/sign-in');
}}
>
Iniciar sesión
</button>
</p>
)}
</nav>
);
};
export default Home;
Punto de control: Prueba tu aplicación
Ahora, puedes probar tu aplicación:
- Ejecuta tu aplicación, verás el botón de inicio de sesión.
- Haz clic en el botón de inicio de sesión, el SDK iniciará el proceso de inicio de sesión y te redirigirá a la página de inicio de sesión de Logto.
- Después de iniciar sesión, serás redirigido de vuelta a tu aplicación y verás el botón de cierre de sesión.
- Haz clic en el botón de cierre de sesión para limpiar el almacenamiento de tokens y cerrar sesión.
Añadir el conector OIDC
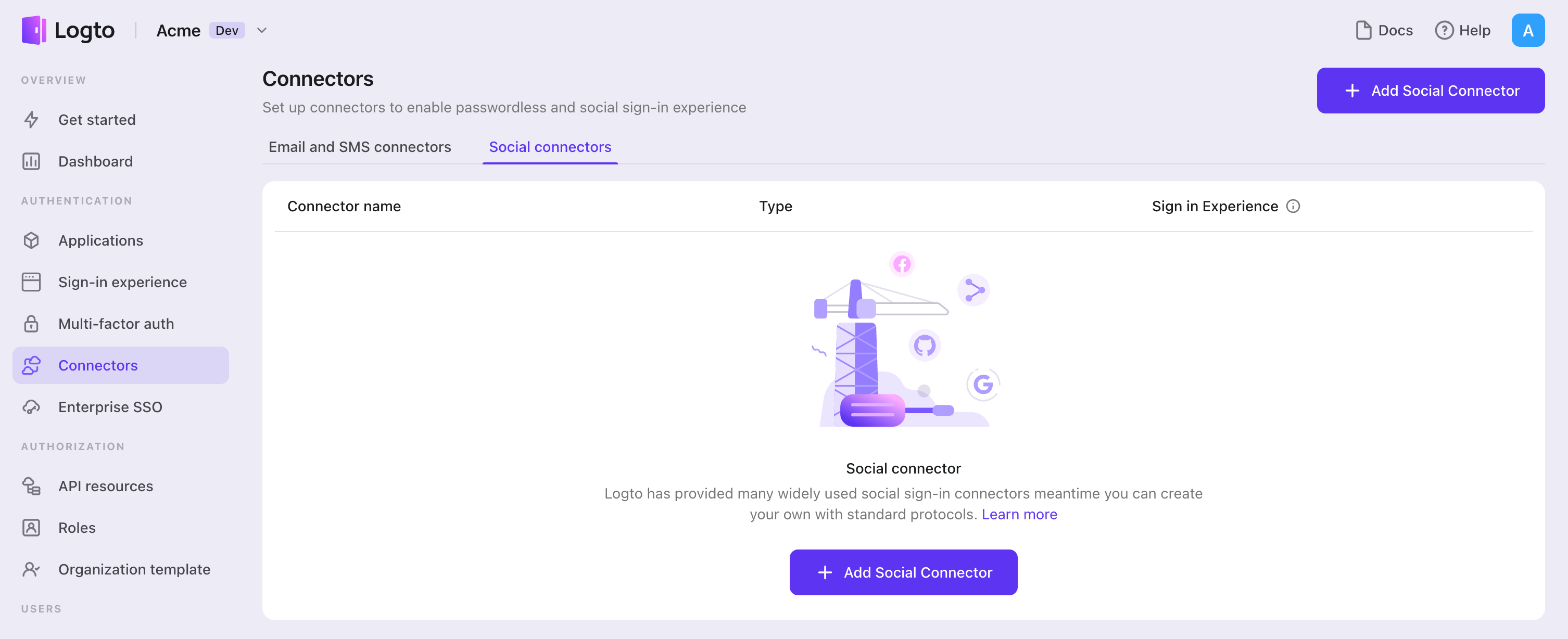
Para habilitar un inicio de sesión rápido y mejorar la conversión de usuarios, conéctate con Next.js como un proveedor de identidad (IdP). El conector social de Logto te ayuda a establecer esta conexión en minutos permitiendo la entrada de varios parámetros.
Para añadir un conector social, simplemente sigue estos pasos:
- Navega a Console > Connectors > Social Connectors.
- Haz clic en "Add social connector" y selecciona "OIDC".
- Sigue la guía README y completa los campos requeridos y personaliza la configuración.
Si estás siguiendo la guía del Conector en el lugar, puedes omitir la siguiente sección.
Configura Aplicación OIDC estándar
Crea tu aplicación OIDC
Cuando abres esta página, creemos que ya sabes qué proveedor de identidad social deseas conectar. Lo primero que debes hacer es confirmar que el proveedor de identidad admite el protocolo OIDC, que es un requisito previo para configurar un conector válido. Luego, sigue las instrucciones del proveedor de identidad para registrar y crear la aplicación relevante para la autorización OIDC.
Configura tu conector
SOLO admitimos el tipo de concesión "Authorization Code" por razones de seguridad y se adapta perfectamente al escenario de Logto.
clientId y clientSecret se pueden encontrar en la página de detalles de tus aplicaciones OIDC.
clientId: El ID de cliente es un identificador único que identifica la aplicación cliente durante el registro con el servidor de autorización. Este ID es utilizado por el servidor de autorización para verificar la identidad de la aplicación cliente y asociar cualquier token de acceso autorizado con esa aplicación cliente específica.
clientSecret: El secreto de cliente es una clave confidencial que se emite a la aplicación cliente por el servidor de autorización durante el registro. La aplicación cliente utiliza esta clave secreta para autenticarse con el servidor de autorización al solicitar tokens de acceso. El secreto de cliente se considera información confidencial y debe mantenerse seguro en todo momento.
tokenEndpointAuthMethod: El método de autenticación del endpoint de token es utilizado por la aplicación cliente para autenticarse con el servidor de autorización al solicitar tokens de acceso. Para descubrir los métodos admitidos, consulta el campo token_endpoint_auth_methods_supported disponible en el endpoint de descubrimiento de OpenID Connect del proveedor de servicios OAuth 2.0, o consulta la documentación relevante proporcionada por el proveedor de servicios OAuth 2.0.
clientSecretJwtSigningAlgorithm (Opcional): Solo se requiere cuando tokenEndpointAuthMethod es client_secret_jwt. El algoritmo de firma JWT del secreto de cliente es utilizado por la aplicación cliente para firmar el JWT que se envía al servidor de autorización durante la solicitud de token.
scope: El parámetro de alcance se utiliza para especificar el conjunto de recursos y permisos a los que la aplicación cliente está solicitando acceso. El parámetro de alcance se define típicamente como una lista de valores separados por espacios que representan permisos específicos. Por ejemplo, un valor de alcance de "read write" podría indicar que la aplicación cliente está solicitando acceso de lectura y escritura a los datos de un usuario.
Se espera que encuentres authorizationEndpoint, tokenEndpoint, jwksUri y issuer como información de configuración del Proveedor de OpenID. Deberían estar disponibles en la documentación del proveedor social.
authenticationEndpoint: Este endpoint se utiliza para iniciar el proceso de autenticación. El proceso de autenticación generalmente implica que el usuario inicie sesión y otorgue autorización para que la aplicación cliente acceda a sus recursos.
tokenEndpoint: Este endpoint es utilizado por la aplicación cliente para obtener un token de ID que se puede usar para acceder a los recursos solicitados. La aplicación cliente generalmente envía una solicitud al endpoint de token con un tipo de concesión y un código de autorización para recibir un token de ID.
jwksUri: Este es el endpoint URL donde se puede obtener el Conjunto de Claves Web JSON (JWKS) del proveedor de identidad social (abreviado como IdP). El JWKS es un conjunto de claves criptográficas que el IdP utiliza para firmar y verificar JSON Web Tokens (JWTs) que se emiten durante el proceso de autenticación. El jwksUri es utilizado por la parte confiable (RP) para obtener las claves públicas utilizadas por el IdP para firmar los JWTs, de modo que la RP pueda verificar la autenticidad e integridad de los JWTs recibidos del IdP.
issuer: Este es el identificador único del IdP que es utilizado por la RP para verificar los JWTs recibidos del IdP. Se incluye en los JWTs como el reclamo iss (el token de ID siempre es un JWT). El valor del emisor debe coincidir con la URL del servidor de autorización del IdP, y debe ser un URI en el que la RP confíe. Cuando la RP recibe un JWT, verifica el reclamo iss para asegurarse de que fue emitido por un IdP confiable y que el JWT está destinado a ser utilizado con la RP.
Juntos, jwksUri y issuer proporcionan un mecanismo seguro para que la RP verifique la identidad del usuario final durante el proceso de autenticación. Al usar las claves públicas obtenidas del jwksUri, la RP puede verificar la autenticidad e integridad de los JWTs emitidos por el IdP. El valor del emisor asegura que la RP solo acepte JWTs que fueron emitidos por un IdP confiable y que los JWTs están destinados a ser utilizados con la RP.
Dado que siempre se requiere una solicitud de autenticación, se proporciona un authRequestOptionalConfig para envolver todas las configuraciones opcionales, puedes encontrar detalles en OIDC Authentication Request. También puedes notar que nonce falta en esta configuración. Dado que nonce debe ser idéntico para cada solicitud, colocamos la generación de nonce en la implementación del código. ¡Así que no te preocupes por ello! Los mencionados anteriormente jwksUri y issuer también están incluidos en idTokenVerificationConfig.
Puede que te preguntes por qué un protocolo OIDC estándar admite tanto los flujos implícitos como los híbridos, pero el conector de Logto solo admite el flujo de autorización. Se ha determinado que los flujos implícitos e híbridos son menos seguros que el flujo de autorización. Debido al enfoque de Logto en la seguridad, solo admite el flujo de autorización para el nivel más alto de seguridad para sus usuarios, a pesar de su naturaleza ligeramente menos conveniente.
responseType y grantType SOLO pueden ser valores FIJOS con el flujo de "Authorization Code", por lo que los hacemos opcionales y los valores predeterminados se completarán automáticamente.
Para todos los tipos de flujo, proporcionamos una clave customConfig OPCIONAL para colocar tus parámetros personalizados.
Cada proveedor de identidad social podría tener su propia variante en el protocolo estándar OIDC. Si tu proveedor de identidad social deseado se adhiere estrictamente al protocolo estándar OIDC, entonces no necesitas preocuparte por customConfig.
Tipos de configuración
| Nombre | Tipo | Requerido |
|---|---|---|
| scope | string | True |
| clientId | string | True |
| clientSecret | string | True |
| authorizationEndpoint | string | True |
| tokenEndpoint | string | True |
| idTokenVerificationConfig | IdTokenVerificationConfig | True |
| authRequestOptionalConfig | AuthRequestOptionalConfig | False |
| customConfig | Record<string, string> | False |
| Propiedades de AuthRequestOptionalConfig | Tipo | Requerido |
|---|---|---|
| responseType | string | False |
| tokenEndpoint | string | False |
| responseMode | string | False |
| display | string | False |
| prompt | string | False |
| maxAge | string | False |
| uiLocales | string | False |
| idTokenHint | string | False |
| loginHint | string | False |
| acrValues | string | False |
| Propiedades de IdTokenVerificationConfig | Tipo | Requerido |
|---|---|---|
| jwksUri | string | True |
| issuer | string | string[] | False |
| audience | string | string[] | False |
| algorithms | string[] | False |
| clockTolerance | string | number | False |
| crit | Record<string, string | boolean> | False |
| currentDate | Date | False |
| maxTokenAge | string | number | False |
| subject | string | False |
| typ | string | False |
Consulta aquí para encontrar más detalles sobre IdTokenVerificationConfig.
Guarda tu configuración
Verifica que hayas completado los valores necesarios en el área de configuración del conector Logto. Haz clic en "Guardar y listo" (o "Guardar cambios") y el conector OIDC debería estar disponible ahora.
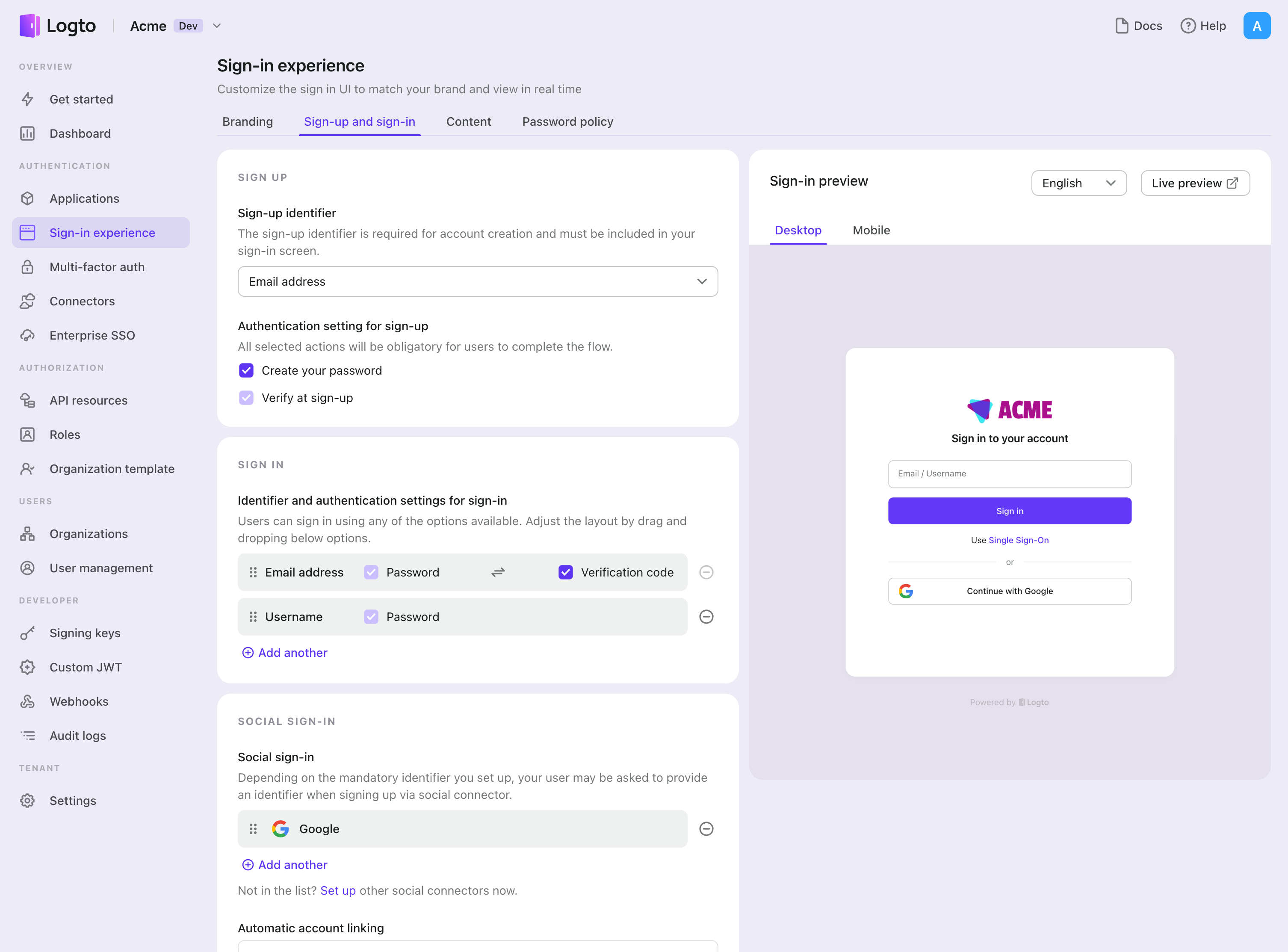
Habilitar el conector OIDC en la Experiencia de inicio de sesión
Una vez que crees un conector social con éxito, puedes habilitarlo como un botón "Continuar con OIDC" en la Experiencia de inicio de sesión.
- Navega a Consola > Experiencia de inicio de sesión > Registro e inicio de sesión.
- (Opcional) Elige "No aplicable" para el identificador de registro si solo necesitas inicio de sesión social.
- Añade el conector OIDC configurado a la sección "Inicio de sesión social".
Pruebas y Validación
Regresa a tu aplicación Next.js (Pages Router). Ahora deberías poder iniciar sesión con OIDC. ¡Disfruta!
Lecturas adicionales
Flujos de usuario final: Logto proporciona flujos de autenticación listos para usar, incluyendo MFA y SSO empresarial, junto con potentes APIs para la implementación flexible de configuraciones de cuenta, verificación de seguridad y experiencia multi-tenant.
Autorización (Authorization): La autorización define las acciones que un usuario puede realizar o los recursos a los que puede acceder después de ser autenticado. Explora cómo proteger tu API para aplicaciones nativas y de una sola página e implementar el Control de Acceso Basado en Roles (RBAC).
Organizaciones (Organizations): Particularmente efectivo en aplicaciones SaaS multi-tenant y B2B, la función de organización permite la creación de inquilinos, gestión de miembros, RBAC a nivel de organización y aprovisionamiento justo a tiempo.
Serie IAM del cliente: Nuestros artículos de blog en serie sobre la Gestión de Identidad y Acceso del Cliente (o Consumidor), desde los conceptos básicos hasta temas avanzados y más allá.