Logto es una alternativa a Auth0 diseñada para aplicaciones modernas y productos SaaS. Ofrece servicios tanto de Cloud como de código abierto para ayudarte a lanzar rápidamente tu sistema de gestión e identidad (IAM). Disfruta de autenticación, autorización y gestión multi-tenant todo en uno.
Recomendamos comenzar con un tenant de desarrollo gratuito en Logto Cloud. Esto te permite explorar todas las características fácilmente.
En este artículo, repasaremos los pasos para construir rápidamente la experiencia de inicio de sesión de Apple (autenticación de usuario) con Vanilla JS y Logto.
Requisitos previos
- Una instancia de Logto en funcionamiento. Consulta la página de introducción para comenzar.
- Conocimientos básicos de Vanilla JS.
- Una cuenta de Apple utilizable.
Crear una aplicación en Logto
Logto se basa en la autenticación OpenID Connect (OIDC) y la autorización OAuth 2.0. Admite la gestión de identidad federada a través de múltiples aplicaciones, comúnmente llamada inicio de sesión único (SSO).
Para crear tu aplicación Single page app, simplemente sigue estos pasos:
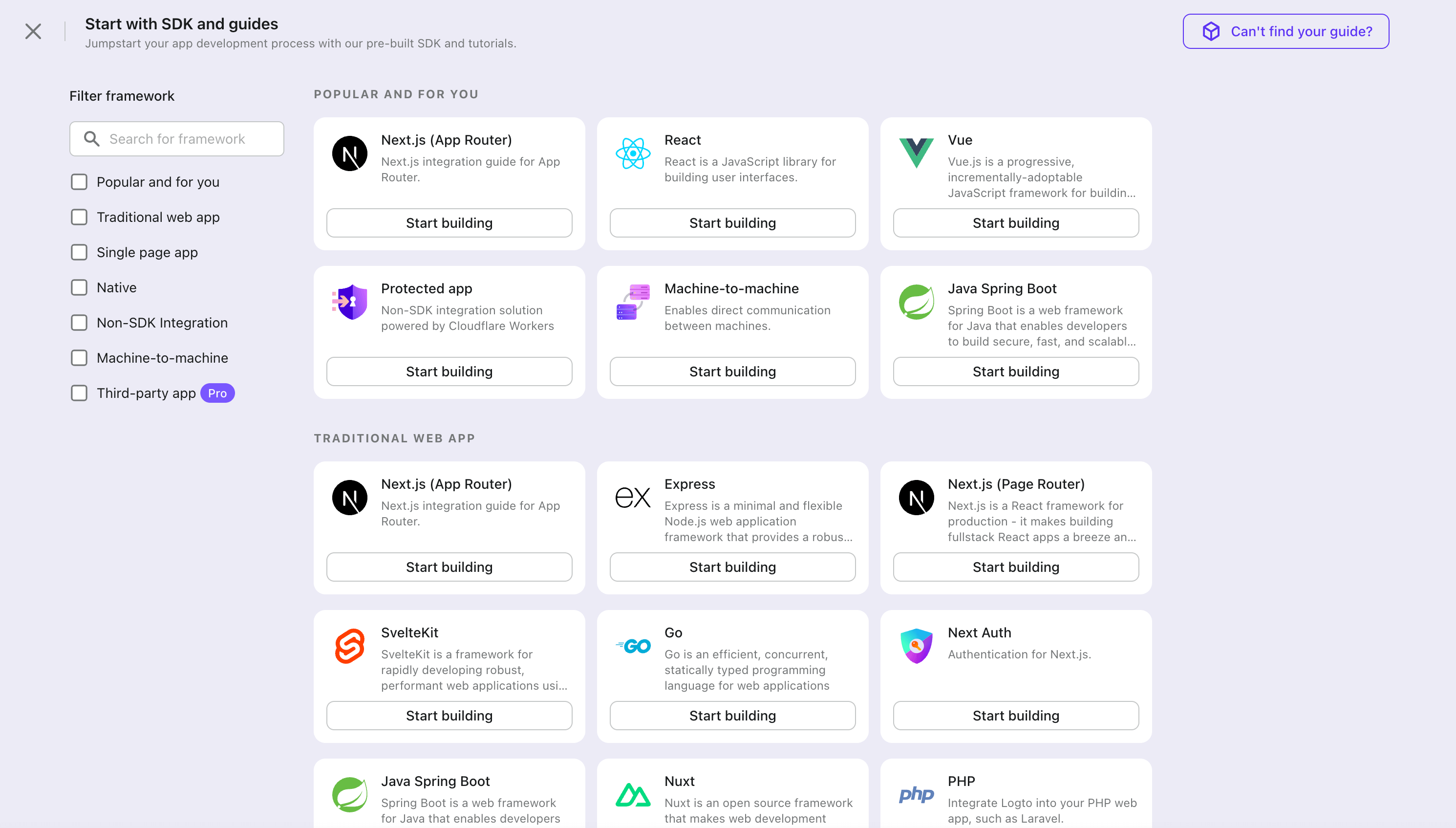
- Abre la Consola de Logto. En la sección "Comenzar", haz clic en el enlace "Ver todo" para abrir la lista de marcos de aplicaciones. Alternativamente, puedes navegar a Consola de Logto > Aplicaciones, y hacer clic en el botón "Crear aplicación".
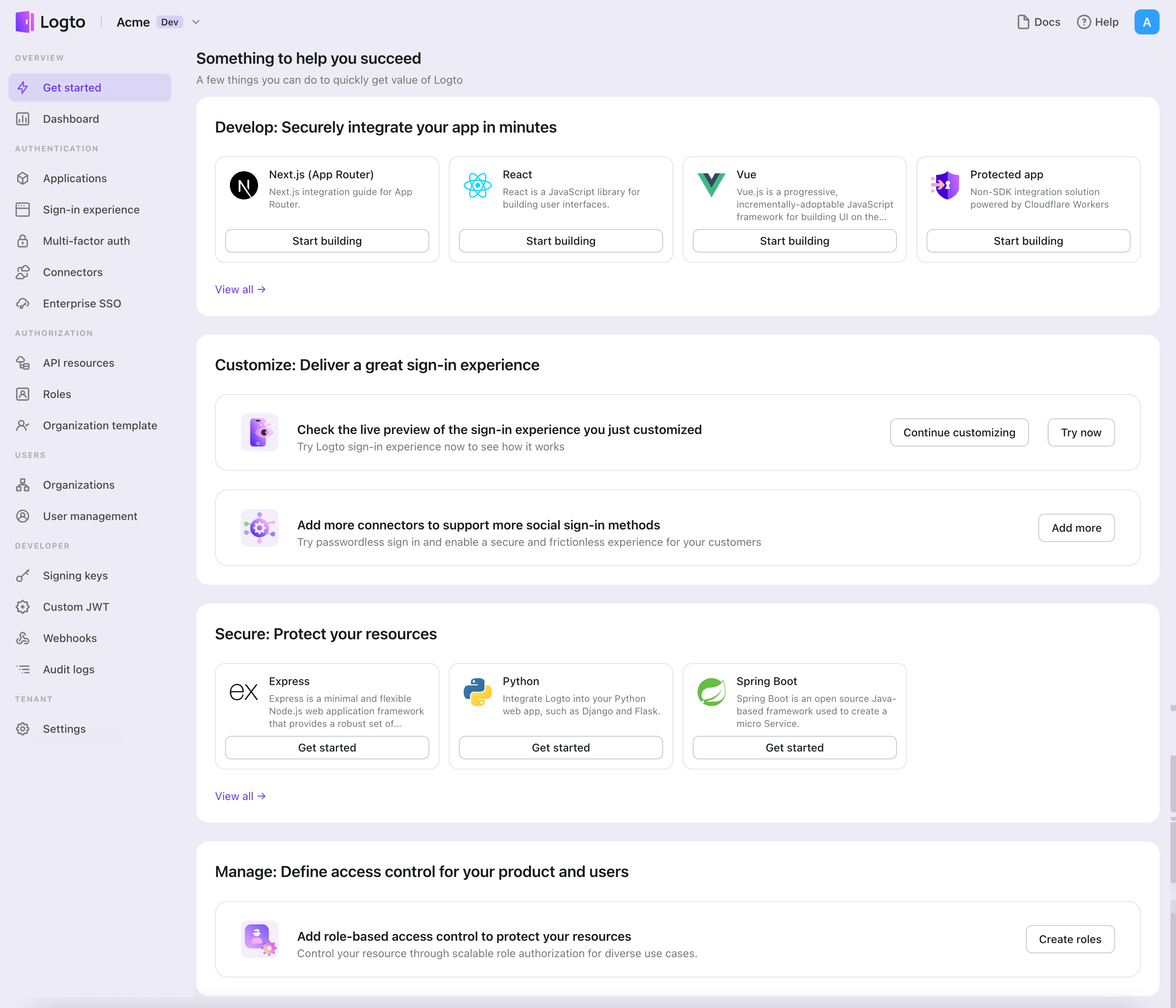
- En el modal que se abre, haz clic en la sección "Single page app" o filtra todos los marcos "Single page app" disponibles usando las casillas de filtro rápido a la izquierda. Haz clic en la tarjeta del marco "Vanilla JS" para comenzar a crear tu aplicación.
- Ingresa el nombre de la aplicación, por ejemplo, "Librería", y haz clic en "Crear aplicación".
🎉 ¡Ta-da! Acabas de crear tu primera aplicación en Logto. Verás una página de felicitaciones que incluye una guía de integración detallada. Sigue la guía para ver cómo será la experiencia en tu aplicación.
Integrar el SDK de Vanilla JS
- El SDK de vanilla-js es independiente del framework, puedes usarlo en cualquier framework frontend escribiendo un envoltorio para adaptarlo.
- El proyecto de ejemplo está disponible en nuestro repositorio de SDK.
Instalación
Elige tu gestor de paquetes favorito o utiliza el CDN para instalar el Logto Browser SDK.
- npm
- pnpm
- yarn
- CDN
npm i @logto/browser
pnpm add @logto/browser
yarn add @logto/browser
<!-- Agradecimientos especiales a jsdelivr -->
<script type="module">
import LogtoClient from 'https://cdn.jsdelivr.net/npm/@logto/[email protected]/+esm';
</script>
Inicializar LogtoClient
Importa e inicia una instancia de LogtoClient pasando la configuración:
import LogtoClient from '@logto/browser';
const logtoClient = new LogtoClient({
endpoint: '<your-logto-endpoint>',
appId: '<your-application-id>',
});
El endpoint y el appId se pueden encontrar en la página de detalles de la aplicación en Logto Console.
Implementar un inicio de sesión y cierre de sesión
Configurar URIs de redirección
Antes de profundizar en los detalles, aquí tienes una visión general rápida de la experiencia del usuario final. El proceso de inicio de sesión se puede simplificar de la siguiente manera:
- Tu aplicación invoca el método de inicio de sesión.
- El usuario es redirigido a la página de inicio de sesión de Logto. Para aplicaciones nativas, se abre el navegador del sistema.
- El usuario inicia sesión y es redirigido de vuelta a tu aplicación (configurada como el URI de redirección).
Sobre el inicio de sesión basado en redirección
- Este proceso de autenticación sigue el protocolo OpenID Connect (OIDC), y Logto aplica medidas de seguridad estrictas para proteger el inicio de sesión del usuario.
- Si tienes múltiples aplicaciones, puedes usar el mismo proveedor de identidad (Logto). Una vez que el usuario inicia sesión en una aplicación, Logto completará automáticamente el proceso de inicio de sesión cuando el usuario acceda a otra aplicación.
Para aprender más sobre la lógica y los beneficios del inicio de sesión basado en redirección, consulta Experiencia de inicio de sesión de Logto explicada.
En los siguientes fragmentos de código, asumimos que tu aplicación está ejecutándose en http://localhost:3000/.
Configurar URIs de redirección
Cambia a la página de detalles de la aplicación en Logto Console. Añade una URI de redirección http://localhost:3000/callback.
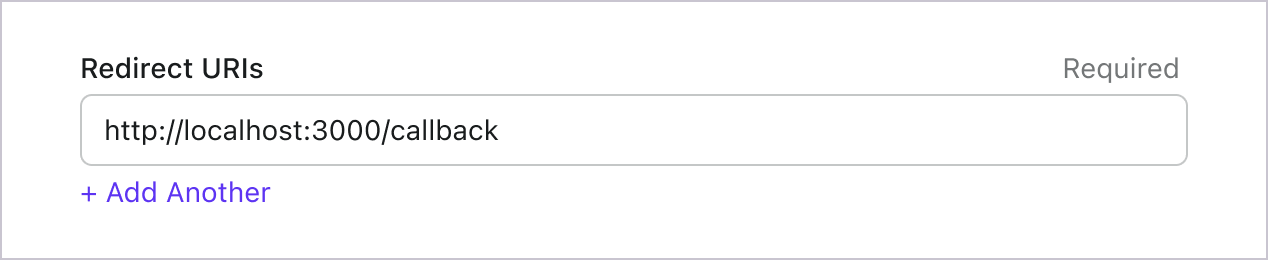
Al igual que al iniciar sesión, los usuarios deben ser redirigidos a Logto para cerrar la sesión de la sesión compartida. Una vez terminado, sería ideal redirigir al usuario de vuelta a tu sitio web. Por ejemplo, añade http://localhost:3000/ como la sección de URI de redirección posterior al cierre de sesión.
Luego haz clic en "Guardar" para guardar los cambios.
Manejar redirección
Todavía hay cosas por hacer después de que el usuario sea redirigido de vuelta a tu aplicación desde Logto. Vamos a manejarlo adecuadamente.
const callbackHandler = async (logtoClient) => {
await logtoClient.handleSignInCallback(window.location.href);
if (!logtoClient.isAuthenticated) {
// Manejar inicio de sesión fallido
alert('Error al iniciar sesión');
return;
}
// Manejar inicio de sesión exitoso
window.location.assign('/');
};
Implementar inicio y cierre de sesión
logtoClient proporciona los métodos signIn y signOut para ayudarte a gestionar fácilmente el flujo de autenticación.
Antes de llamar a .signIn(), asegúrate de haber configurado correctamente el URI de redirección en la Consola de Administración.
const isAuthenticated = await logtoClient.isAuthenticated();
const onClickSignIn = () => {
logtoClient.signIn('http://localhost:3000/callback');
};
const onClickSignOut = () => {
logtoClient.signOut('http://localhost:3000');
};
const button = document.createElement('button');
button.innerHTML = isAuthenticated ? 'Sign Out' : 'Sign In';
button.addEventListener('click', isAuthenticated ? onClickSignOut : onClickSignIn);
document.body.appendChild(button);
Llamar a .signOut() borrará todos los datos de Logto en la memoria y en localStorage si existen.
Manejar el estado de autenticación
En Logto SDK, generalmente podemos usar logtoClient.isAuthenticated para verificar el estado de autenticación. Si el usuario ha iniciado sesión, el valor será true, de lo contrario, el valor será false.
En tu aplicación JS vanilla, puedes usar el estado isAuthenticated para mostrar y ocultar programáticamente los botones de inicio y cierre de sesión. Veamos cómo hacerlo.
const redirectUrl = 'http://localhost:3000/callback';
const baseUrl = 'http://localhost:3000';
// Renderizado condicional de los botones de inicio y cierre de sesión
const render = async (logtoClient) => {
const isAuthenticated = await logtoClient.isAuthenticated();
const container = document.querySelector('#container');
const onClickSignIn = () => logtoClient.signIn(redirectUrl);
const onClickSignOut = () => logtoClient.signOut(baseUrl);
const button = document.createElement('button');
button.innerHTML = isAuthenticated ? 'Sign Out' : 'Sign In';
button.addEventListener('click', isAuthenticated ? onClickSignOut : onClickSignIn);
container.append(button);
};
Punto de control: Prueba tu aplicación
Ahora, puedes probar tu aplicación:
- Ejecuta tu aplicación, verás el botón de inicio de sesión.
- Haz clic en el botón de inicio de sesión, el SDK iniciará el proceso de inicio de sesión y te redirigirá a la página de inicio de sesión de Logto.
- Después de iniciar sesión, serás redirigido de vuelta a tu aplicación y verás el botón de cierre de sesión.
- Haz clic en el botón de cierre de sesión para limpiar el almacenamiento de tokens y cerrar sesión.
Añadir el conector Apple
Para habilitar un inicio de sesión rápido y mejorar la conversión de usuarios, conéctate con Vanilla JS como un proveedor de identidad (IdP). El conector social de Logto te ayuda a establecer esta conexión en minutos permitiendo la entrada de varios parámetros.
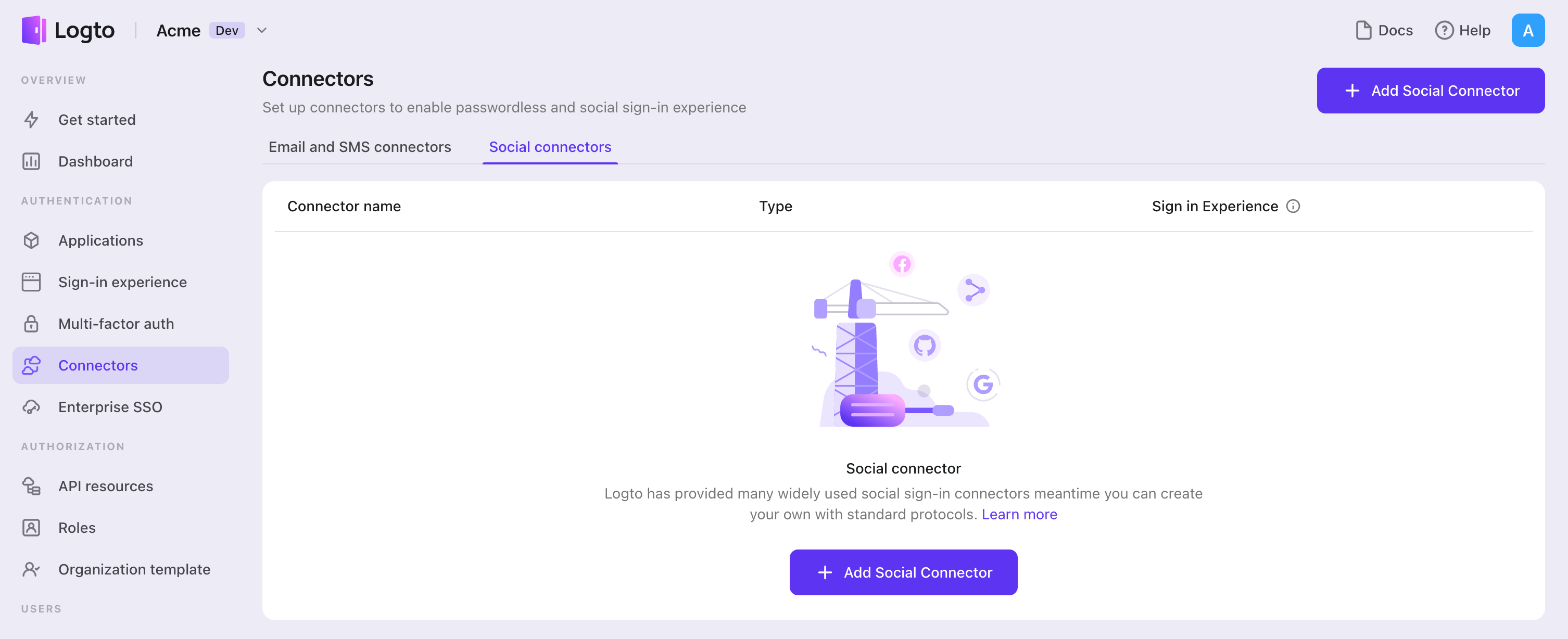
Para añadir un conector social, simplemente sigue estos pasos:
- Navega a Console > Connectors > Social Connectors.
- Haz clic en "Add social connector" y selecciona "Apple".
- Sigue la guía README y completa los campos requeridos y personaliza la configuración.
Si estás siguiendo la guía del Conector en el lugar, puedes omitir la siguiente sección.
Configura Apple Sign-in
El inicio de sesión con Apple es obligatorio para AppStore si tienes otros métodos de inicio de sesión social en tu aplicación. Tener inicio de sesión con Apple en dispositivos Android es excelente si también ofreces una aplicación para Android.
Necesitas inscribirte en el Apple Developer Program antes de continuar.
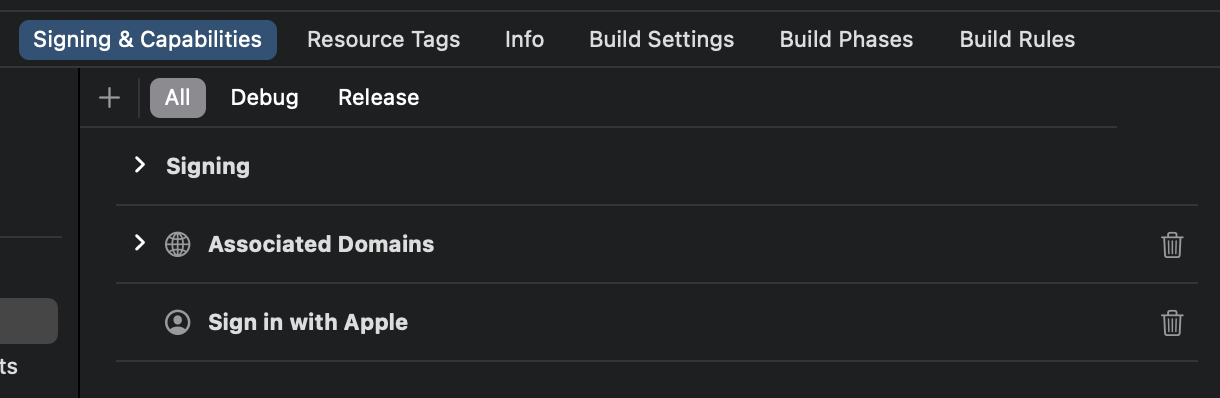
Habilitar el inicio de sesión con Apple para tu aplicación
Incluso si deseas implementar el inicio de sesión con Apple solo en una aplicación web, aún necesitas tener una aplicación existente que abrace el ecosistema de AppStore (es decir, tener un ID de aplicación válido).
Puedes hacerlo a través de Xcode -> Configuración del proyecto -> Firmado y Capacidades, o visitar Certificates, Identifiers & Profiles.
Consulta la sección "Habilitar un ID de aplicación" en los documentos oficiales de Apple para más información.
Crear un identificador
- Visita Certificates, Identifiers & Profiles, luego haz clic en el botón "+" junto a "Identifier".
- En la página "Registrar un nuevo identificador", elige "Services IDs" y haz clic en "Continue".
- Completa "Description" e "Identifier" (Ej.,
Logto Testyio.logto.test), luego haz clic en "Continue". - Verifica la información y haz clic en "Register".
Habilitar el inicio de sesión con Apple para tu identificador
Haz clic en el identificador que acabas de crear. Marca "Sign in with Apple" en la página de detalles y haz clic en "Configure".
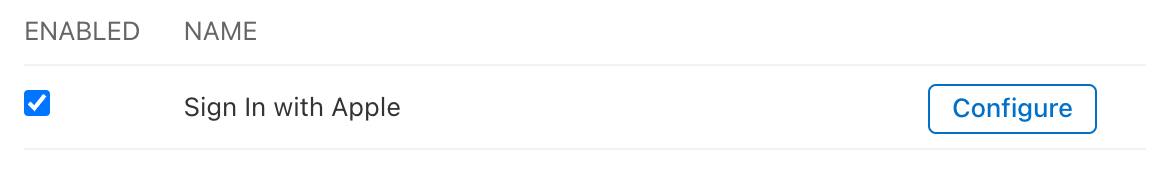
En el modal que se abre, selecciona el ID de aplicación al que acabas de habilitar el inicio de sesión con Apple.
Ingresa el dominio de tu instancia de Logto sin protocolo ni puerto, por ejemplo, your.logto.domain; luego ingresa la "Return URL" (es decir, Redirect URI), que es la URL de Logto con /callback/${connector_id}, por ejemplo, https://your.logto.domain/callback/apple-universal. Puedes obtener el connector_id generado aleatoriamente después de crear el conector de Apple en la Consola de Administración.
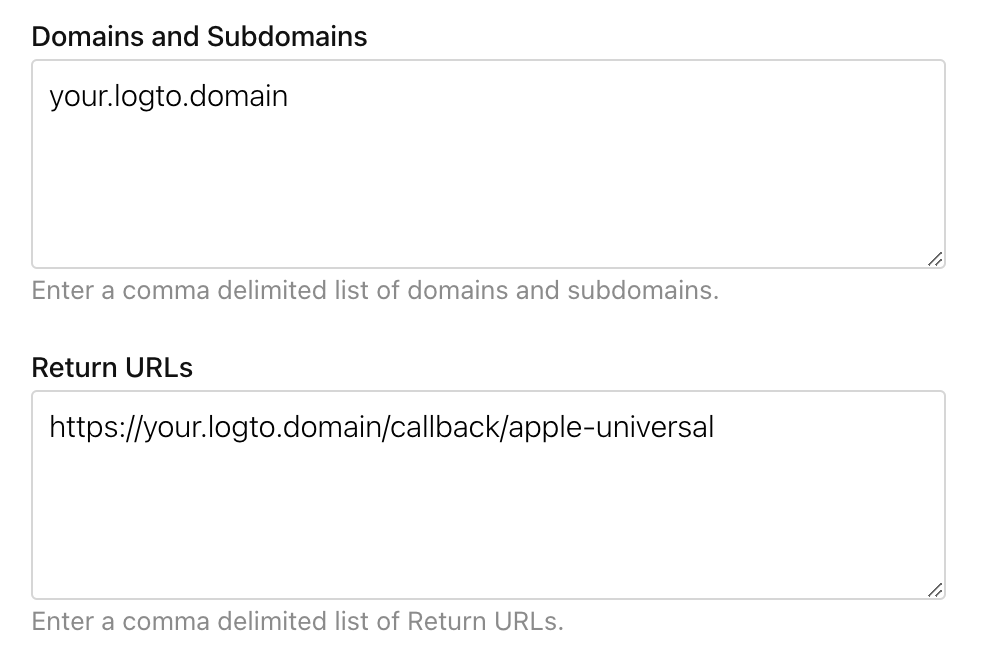
Haz clic en "Next" y luego en "Done" para cerrar el modal. Haz clic en "Continue" en la esquina superior derecha, luego haz clic en "Save" para guardar tu configuración.
Apple NO permite URLs de retorno con protocolo HTTP y dominio localhost.
Si deseas probar localmente, necesitas editar el archivo /etc/hosts para mapear localhost a un dominio personalizado y configurar un entorno HTTPS local. mkcert puede ayudarte a configurar HTTPS local.
Configurar alcance
Para obtener el correo electrónico del usuario de Apple, necesitas configurar el alcance para incluir email. Para obtener tanto el correo electrónico como el nombre, puedes usar name email como el alcance. Consulta los documentos oficiales de Apple para más información.
El usuario puede optar por ocultar su dirección de correo electrónico de tu aplicación. En este caso, no podrás recuperar la dirección de correo electrónico real. En su lugar, se devolverá una dirección de correo electrónico como [email protected].
Guarda tu configuración
Verifica que hayas completado los valores necesarios en el área de configuración del conector Logto. Haz clic en "Guardar y listo" (o "Guardar cambios") y el conector Apple debería estar disponible ahora.
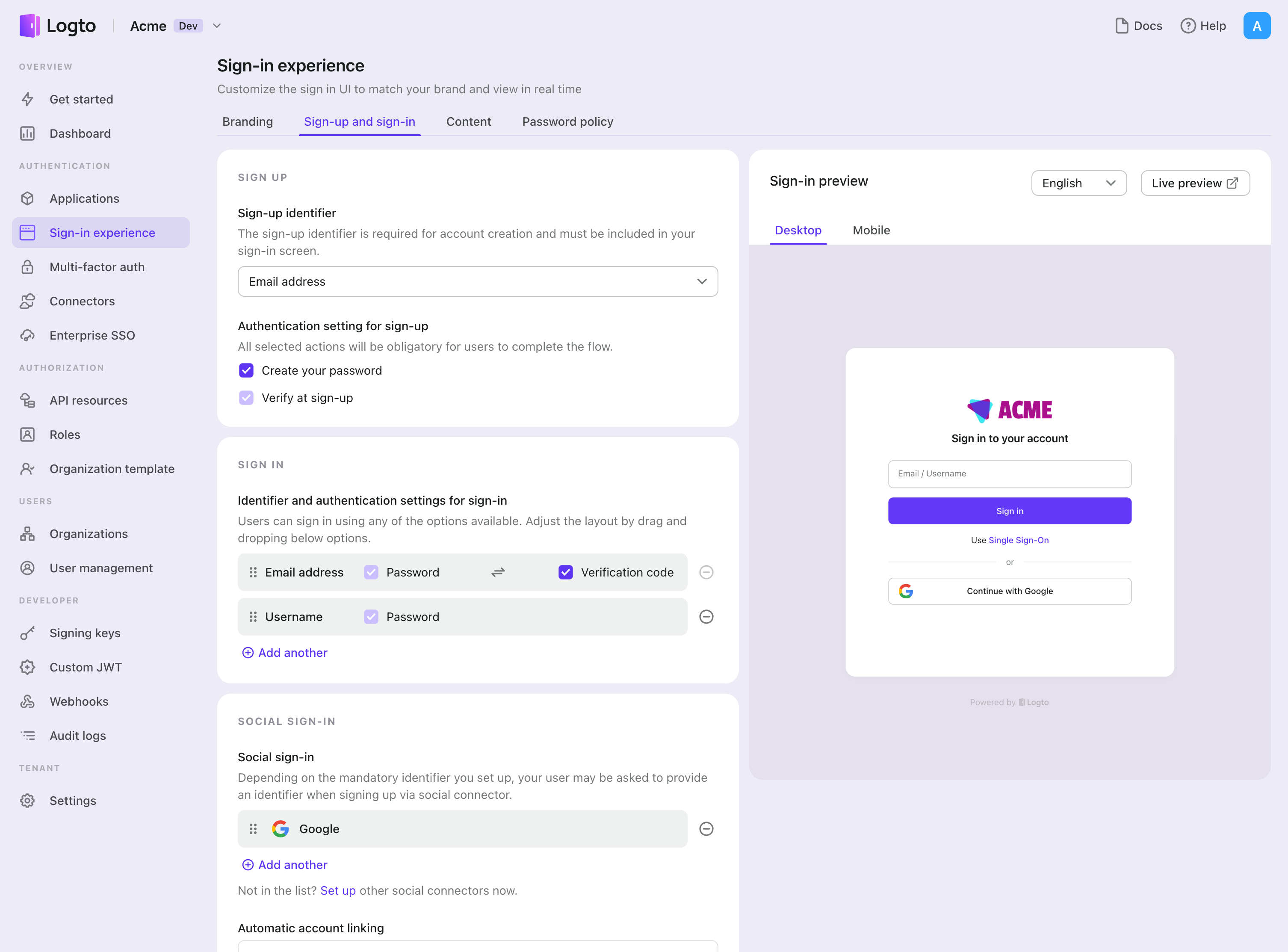
Habilitar el conector Apple en la Experiencia de inicio de sesión
Una vez que crees un conector social con éxito, puedes habilitarlo como un botón "Continuar con Apple" en la Experiencia de inicio de sesión.
- Navega a Consola > Experiencia de inicio de sesión > Registro e inicio de sesión.
- (Opcional) Elige "No aplicable" para el identificador de registro si solo necesitas inicio de sesión social.
- Añade el conector Apple configurado a la sección "Inicio de sesión social".
Pruebas y Validación
Regresa a tu aplicación Vanilla JS. Ahora deberías poder iniciar sesión con Apple. ¡Disfruta!
Lecturas adicionales
Flujos de usuario final: Logto proporciona flujos de autenticación listos para usar, incluyendo MFA y SSO empresarial, junto con potentes APIs para la implementación flexible de configuraciones de cuenta, verificación de seguridad y experiencia multi-tenant.
Autorización (Authorization): La autorización define las acciones que un usuario puede realizar o los recursos a los que puede acceder después de ser autenticado. Explora cómo proteger tu API para aplicaciones nativas y de una sola página e implementar el Control de Acceso Basado en Roles (RBAC).
Organizaciones (Organizations): Particularmente efectivo en aplicaciones SaaS multi-tenant y B2B, la función de organización permite la creación de inquilinos, gestión de miembros, RBAC a nivel de organización y aprovisionamiento justo a tiempo.
Serie IAM del cliente: Nuestros artículos de blog en serie sobre la Gestión de Identidad y Acceso del Cliente (o Consumidor), desde los conceptos básicos hasta temas avanzados y más allá.