Every app needs authentication and authorization. Logto is an Auth0 alternative designed for modern apps and SaaS products.
In this article, we will go through the steps to quickly build the OAuth2 sign-in experience (user authentication) with React and Logto.
Prerequisites
- A running Logto instance. Check out the get started page if you don't have one.
- Basic knowledge of React.
- A usable OAuth2 account.
Create an application in Logto
In you browser, open a new tab and enter the link of Logto Admin Console.
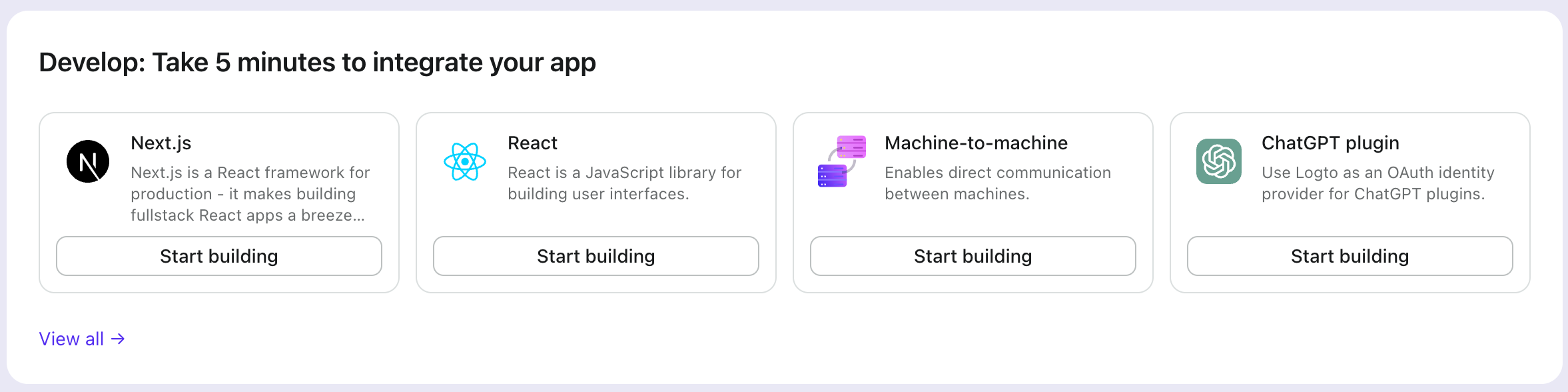
Once the page is loaded, in the "Get Started" section click the View all link to open the application framework list page.
Choose your application type
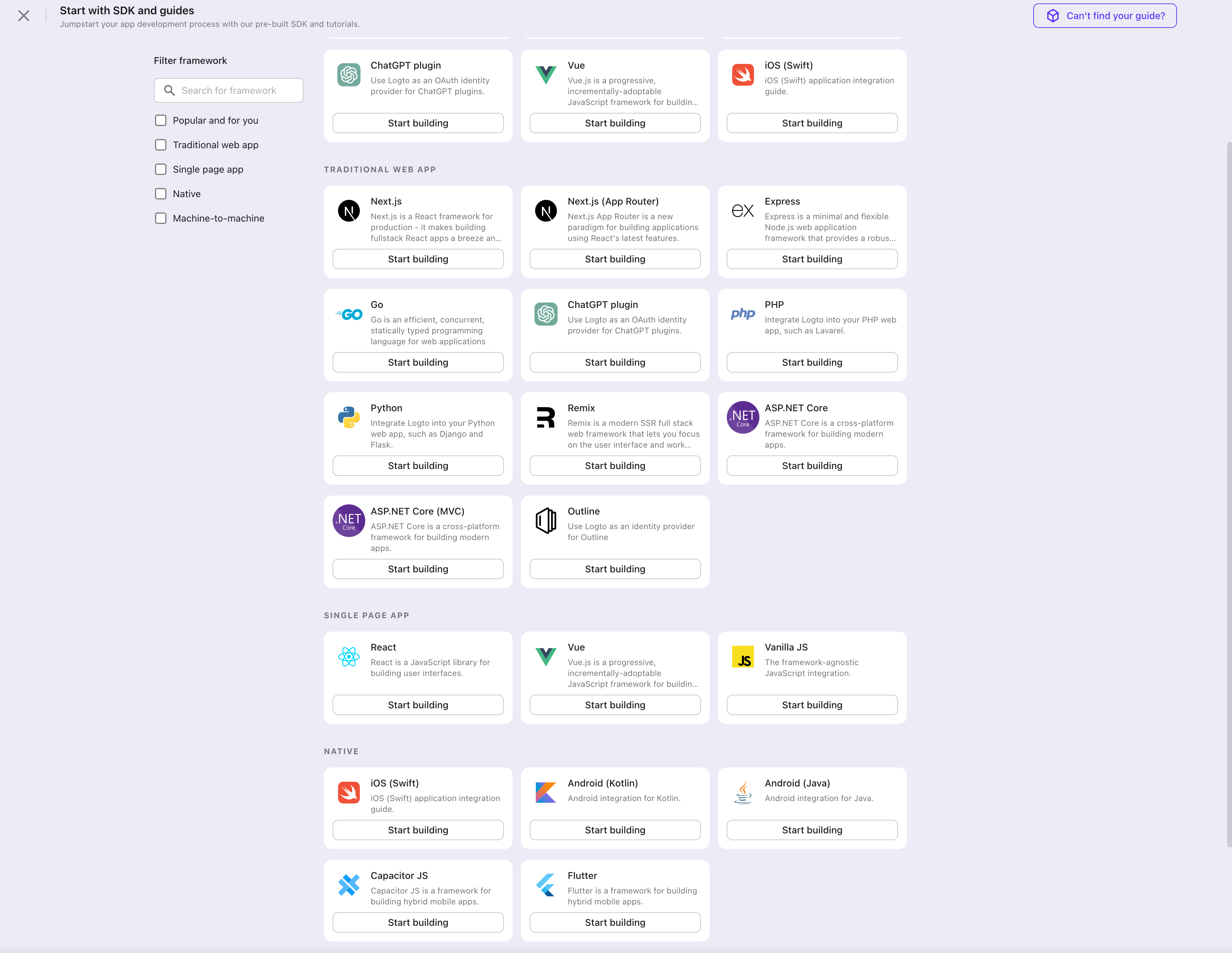
In the opening modal, scroll to the "Single page app" section or filter all the available " Single page app" frameworks using the quick filter checkboxes on the left.
Click the "React" framework card to start creating your application.
Enter application name
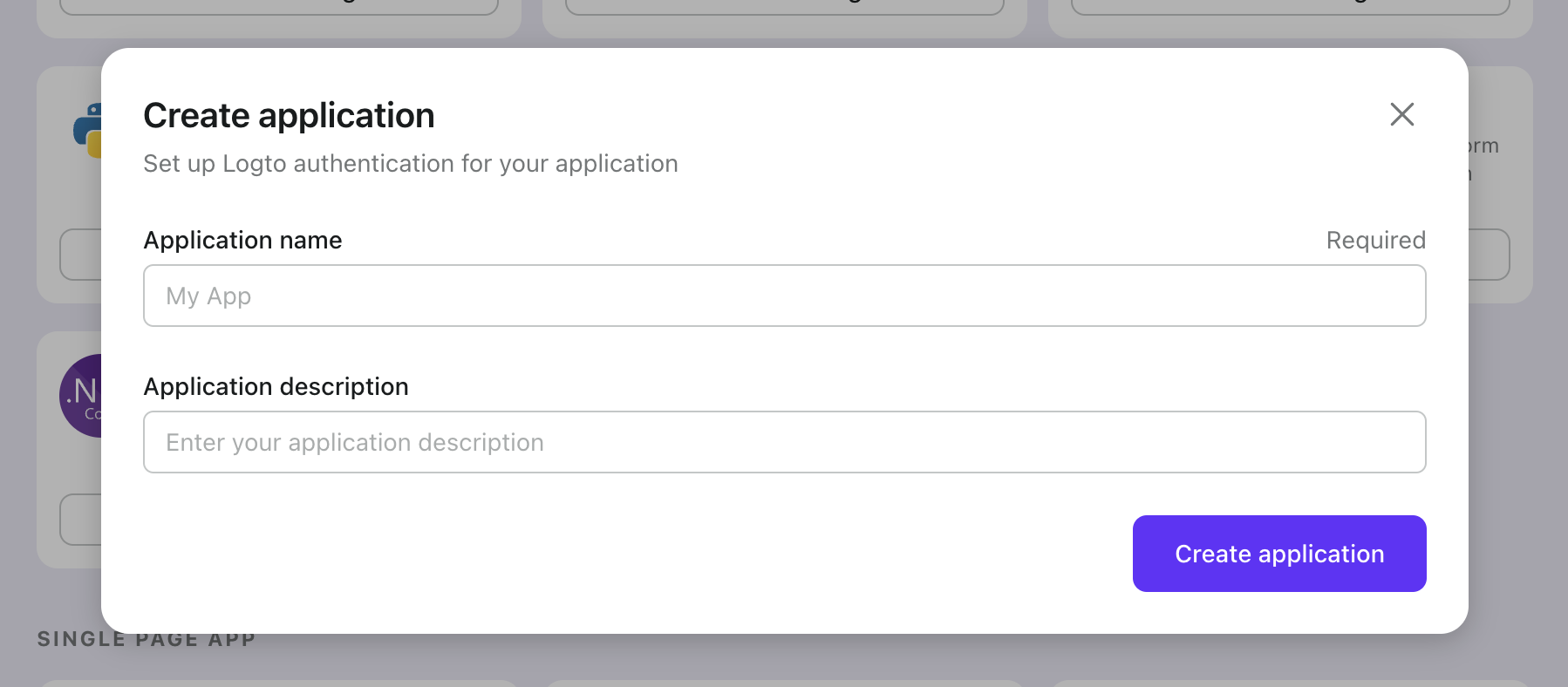
Enter the application name, e.g., "Bookstore," and click "Create Application."
🎉 Ta-da! You just created your first application in Logto. You'll see a congrats page which includes a detailed integration guide. Follow the guide to see what the experience will be in your application.
Integrate Logto SDK
- The sample project is available on our SDK repository.
- The tutorial video is available on our YouTube channel.
Installation
- npm
- Yarn
- pnpm
npm i @logto/react
yarn add @logto/react
pnpm add @logto/react
Init LogtoClient
In the following code snippets, we assume your app is running on http://localhost:3000.
Import and use LogtoProvider to provide a Logto context:
import { LogtoProvider, LogtoConfig } from '@logto/react';
const config: LogtoConfig = {
endpoint: '<your-logto-endpoint>', // E.g. http://localhost:3001
appId: '<your-application-id>',
};
const App = () => (
<LogtoProvider config={config}>
<YourAppContent />
</LogtoProvider>
);
Implement sign-in
The sign-in flow can be simplified as:
Configure sign-in redirect URI
Let's switch to the Application details page of Logto Console. Add a Redirect URI
http://localhost:3000/callback and click "Save Changes".
Redirect URI is an OAuth 2.0 concept which implies the location should redirect after authentication.
Implement a sign-in button
We provide two hooks useHandleSignInCallback() and useLogto() which can help you easily manage the authentication flow.
Before calling .signIn(), make sure you have correctly configured Redirect URI
in Admin Console.
Go back to your IDE/editor, use the following code to implement the sign-in button:
import { useLogto } from '@logto/react';
const SignIn = () => {
const { signIn, isAuthenticated } = useLogto();
if (isAuthenticated) {
return <div>Signed in</div>;
}
return <button onClick={() => signIn('http://localhost:3000/callback')}>Sign In</button>;
};
Handle redirect
We're almost there! In the last step, we use http://localhost:3000/callback as the Redirect URI, and now we need to handle it properly.
First let's create a callback component:
import { useHandleSignInCallback } from '@logto/react';
const Callback = () => {
const { isLoading } = useHandleSignInCallback(() => {
// Navigate to root path when finished
});
// When it's working in progress
if (isLoading) {
return <div>Redirecting...</div>;
}
return null;
};
Finally insert the code below to create a /callback route which does NOT require authentication:
// Assuming react-router
<Route path="/callback" element={<Callback />} />
Implement sign-out
Calling .signOut() will clear all the Logto data in memory and localStorage if they exist.
After signing out, it'll be great to redirect your user back to your website. Let's add http://localhost:3000 as one of the Post Sign-out URIs in Admin Console (shows under Redirect URIs), and use the URL as the parameter when calling .signOut().
Implement a sign-out button
const SignOut = () => {
const { signOut } = useLogto();
return <button onClick={() => signOut('http://localhost:3000')}>Sign out</button>;
};
Handle authentication status
In Logto SDK, generally we can use logtoClient.isAuthenticated to check the authentication status, if the user is signed in, the value will be true, otherwise, the value will be false.
In Logto React SDK, the isAuthenticated status can be checked by using the useLogto hook. In the example code below, we can use it to programmatically show and hide the sign-in and sign-out buttons. And also use getIdTokenClaims to get the id of the currently logged-in user.
const Home = () => {
const { isAuthenticated, getIdTokenClaims, signIn, signOut } = useLogto();
const [userId, setUserId] = useState('');
useEffect(() => {
(async () => {
if (isAuthenticated) {
const claims = await getIdTokenClaims();
setUserId(claims.sub);
}
})();
}, [isAuthenticated]);
return (
<div>
{userId && <p>Logged in as {userId}</p>}
{isAuthenticated ? (
<button onClick={signOut}>Sign Out</button>
) : (
<button onClick={() => signIn('http://localhost:3000/callback')}>Sign In</button>
)}
</div>
);
};
Open your React app to test if the integration works. When you click the "Sign In" button, the page should be redirected to a Logto sign-in page, and you should be able to create a new account by entering username and password and complete the sign-in process.
Add OAuth2 connector
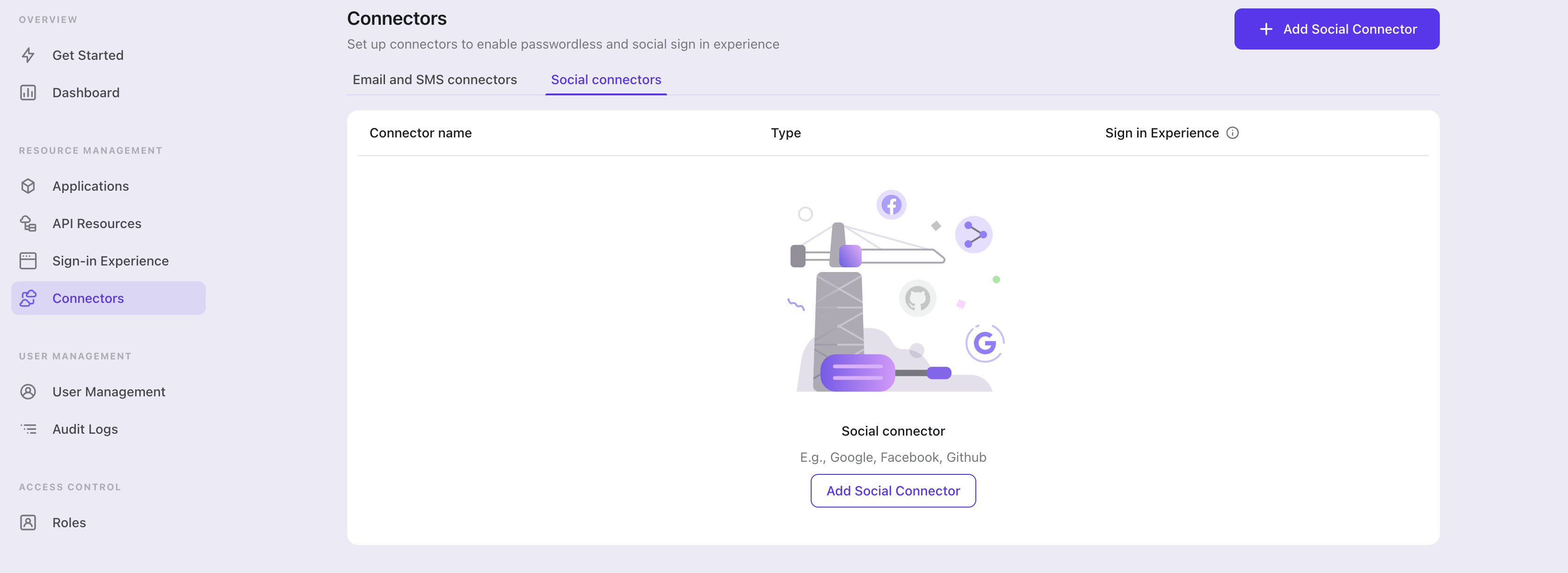
To add a social connector, go to the "Connector" tab in the Admin Console, then click on "Social Connectors". From there, click "Add Social Connector".
In the openning modal, select "OAuth2" and click "Next".
On the next page, you will see a two-column layout with the README content on the left and configuration on the right.
Feel free to follow the README file in place or read the following section to complete the configuration process. If you follow the in-place guide, you can skip the next section.
Set up Standard OAuth 2.0 app
Create your OAuth 2.0 app
When you open this page, we believe you already know which social identity provider you want to connect to. The first thing to do is to confirm that the identity provider supports the OAuth 2.0 protocol, which is a prerequisite for configuring a valid connector. Then, follow the identity provider's instructions to register and create the relevant app for OAuth 2.0 authorization.
Configure your connector
We ONLY support "Authorization Code" grant type for security consideration and it can perfectly fit Logto's scenario.
clientId and clientSecret can be found at your OAuth 2.0 apps details page.
clientId: The client ID is a unique identifier that identifies the client application during registration with the authorization server. This ID is used by the authorization server to verify the identity of the client application and to associate any authorized access tokens with that specific client application.
clientSecret: The client secret is a confidential key that is issued to the client application by the authorization server during registration. The client application uses this secret key to authenticate itself with the authorization server when requesting access tokens. The client secret is considered confidential information and should be kept secure at all times.
scope: The scope parameter is used to specify the set of resources and permissions that the client application is requesting access to. The scope parameter is typically defined as a space-separated list of values that represent specific permissions. For example, a scope value of "read write" might indicate that the client application is requesting read and write access to a user's data.
You are expected to find authorizationEndpoint, tokenEndpoint and userInfoEndpoint in social vendor's documentation.
authenticationEndpoint: This endpoint is used to initiate the authentication process. The authentication process typically involves the user logging in and granting authorization for the client application to access their resources.
tokenEndpoint: This endpoint is used by the client application to obtain an access token that can be used to access the requested resources. The client application typically sends a request to the token endpoint with a grant type and authorization code to receive an access token.
userInfoEndpoint: This endpoint is used by the client application to obtain additional information about the user, such as their fullname, email address or profile picture. The user info endpoint is typically accessed after the client application has obtained an access token from the token endpoint.
Logto also provide a profileMap field that users can customize the mapping from the social vendors' profiles which are usually not standard. The keys are Logto's standard user profile field names and corresponding values should be social profiles' field names. In current stage, Logto only concern 'id', 'name', 'avatar', 'email' and 'phone' from social profile, only 'id' is required and others are optional fields.
responseType and grantType can ONLY be FIXED values with authorization code grant type, so we make them optional and default values will be automatically filled.
For example, you can find Google user profile response and hence its profileMap should be like:
{
"id": "sub",
"avatar": "picture"
}
ℹ️ Note
We provided an OPTIONAL
customConfigkey to put your customize parameters. Each social identity provider could have their own variant on OAuth 2.0 standard protocol. If your desired social identity provider strictly stick to OAuth 2.0 standard protocol, the you do not need to care aboutcustomConfig.
Config types
| Name | Type | Required |
|---|---|---|
| authorizationEndpoint | string | true |
| userInfoEndpoint | string | true |
| clientId | string | true |
| clientSecret | string | true |
| tokenEndpointResponseType | enum | false |
| responseType | string | false |
| grantType | string | false |
| tokenEndpoint | string | false |
| scope | string | false |
| customConfig | { [key: string]: string } | false |
| profileMap | ProfileMap | false |
| ProfileMap fields | Type | Required | Default value |
|---|---|---|---|
| id | string | false | id |
| name | string | false | name |
| avatar | string | false | avatar |
| string | false | ||
| phone | string | false | phone |
Reference
Save your configuration
Double check you have filled out necessary values in the Logto connector configuration area. Click "Save and Done" (or "Save Changes") and the OAuth2 connector should be available now.
Enable OAuth2 connector in Sign-in Experience
Switch to the "Sign-in Experience" tab, then click the "Sign-up and Sign-in" tab.
If it's the first time you enter the tab, you will see a quick introduction about Sign-in Experience and its basic configuration.
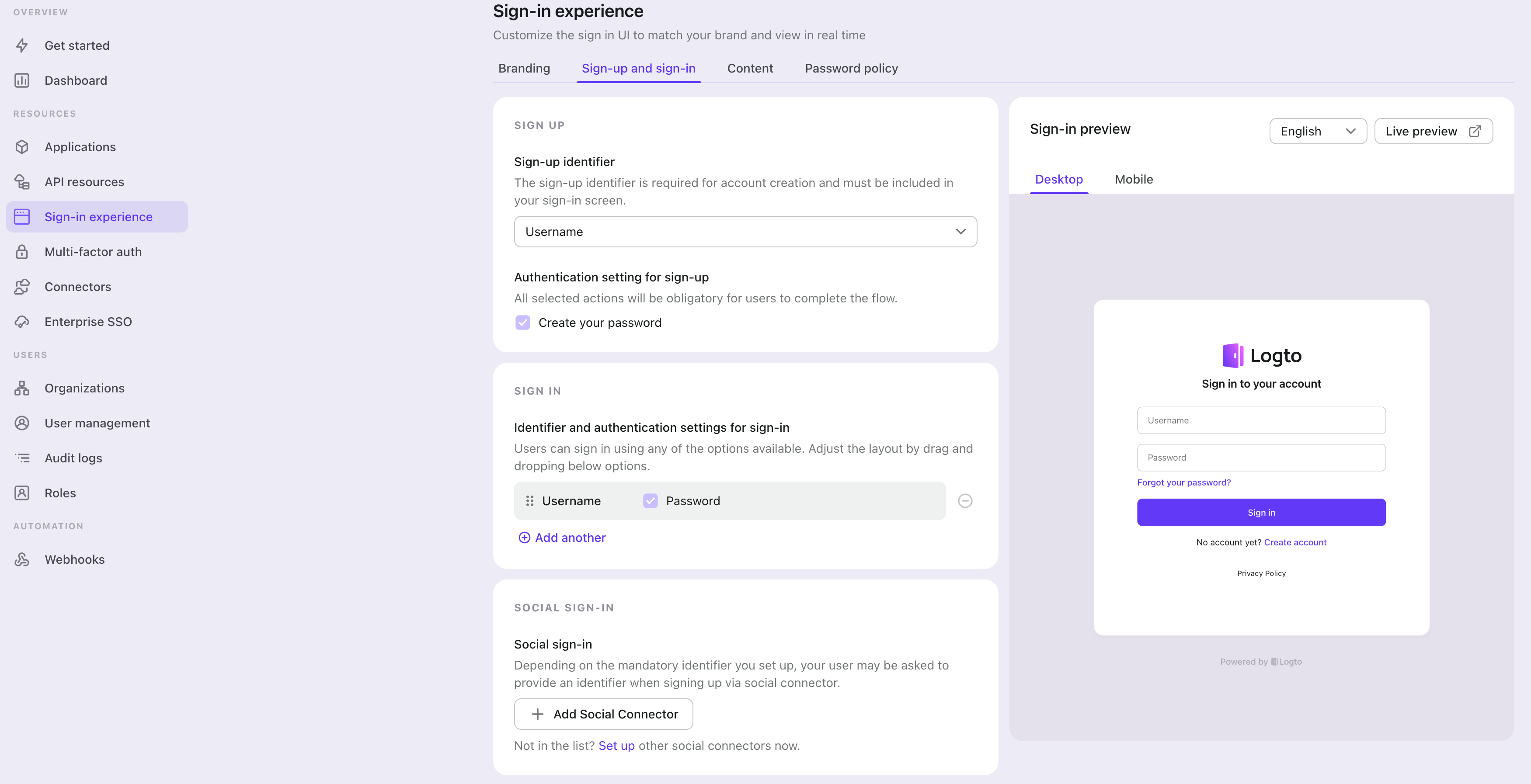
Select "None" for the "Sign-up identifier" to provide minimum sign-up effort for OAuth2 sign-in, which may increase your conversion rate.
In the "Social sign-in" section, add "Add Social Connector" and choose "OAuth2". Then you should be able to see a button with text "Continue with OAuth2" in the preview section.
Finally, click "Save Changes" on the bottom right corner.
Testing and Validation
Return to your React app. You should now be able to sign in with OAuth2. Enjoy!
Further readings
⚔️ Protect your API For native and single page apps, you'll need to call one or more API endpoints to retrieve and update data.
Learn more about identifying who's who and keeping your API secure.
🧑🚀 Manage users We know you care about user management and activities, as we also do.
Learn more about how to know your users and see the figures like DAU and MAU graphically.
🌐 Localization From one regional business to a global corporate, the willingness to offer the best user experience won't change.
You can change current language phrases or add a new language without friction.
🧑🎓 Customer IAM series Our serial blog posts about Customer (or Consumer) Identity and Access Management, from 101 to advanced topics and beyond.